
Revolutionizing Cybersecurity: The Theory of Infinite Keys and Variable States
Introduction
In an age where cyber threats are becoming increasingly sophisticated, businesses and municipalities are prime targets for persistent attacks. Behind these threats lies a repetition of attempts and learning mechanisms exploited by attackers.
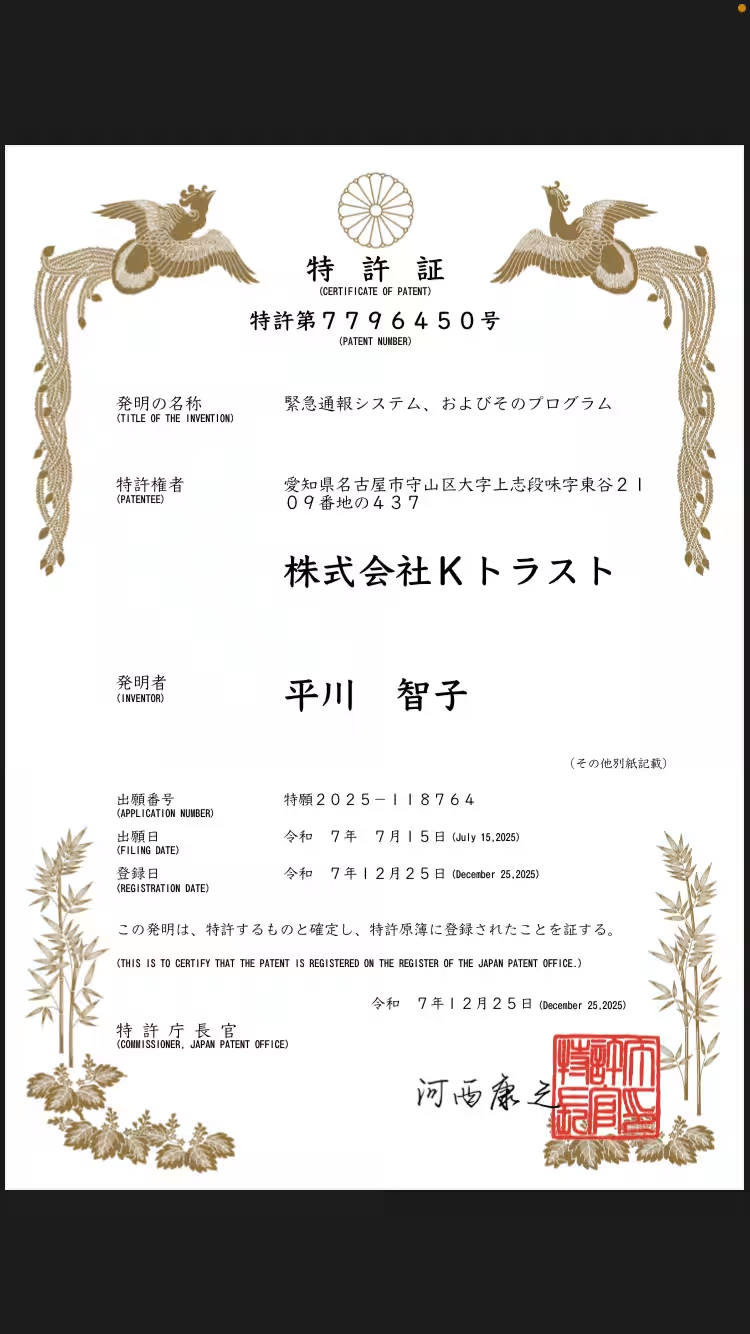
As part of this evolving landscape, the Point Organization Inc., headquartered in Shibuya, Tokyo, is collaborating with K-Trust Inc. from Nagoya to develop a groundbreaking theory: the "Theory of Infinite Keys and Variable States." This new approach aims to redefine security measures, and a patent application is currently underway, with some elements already secured under patent. This article delves into the weaknesses of traditional security systems and elucidates the societal applications of this new framework.
Traditional Security Weaknesses
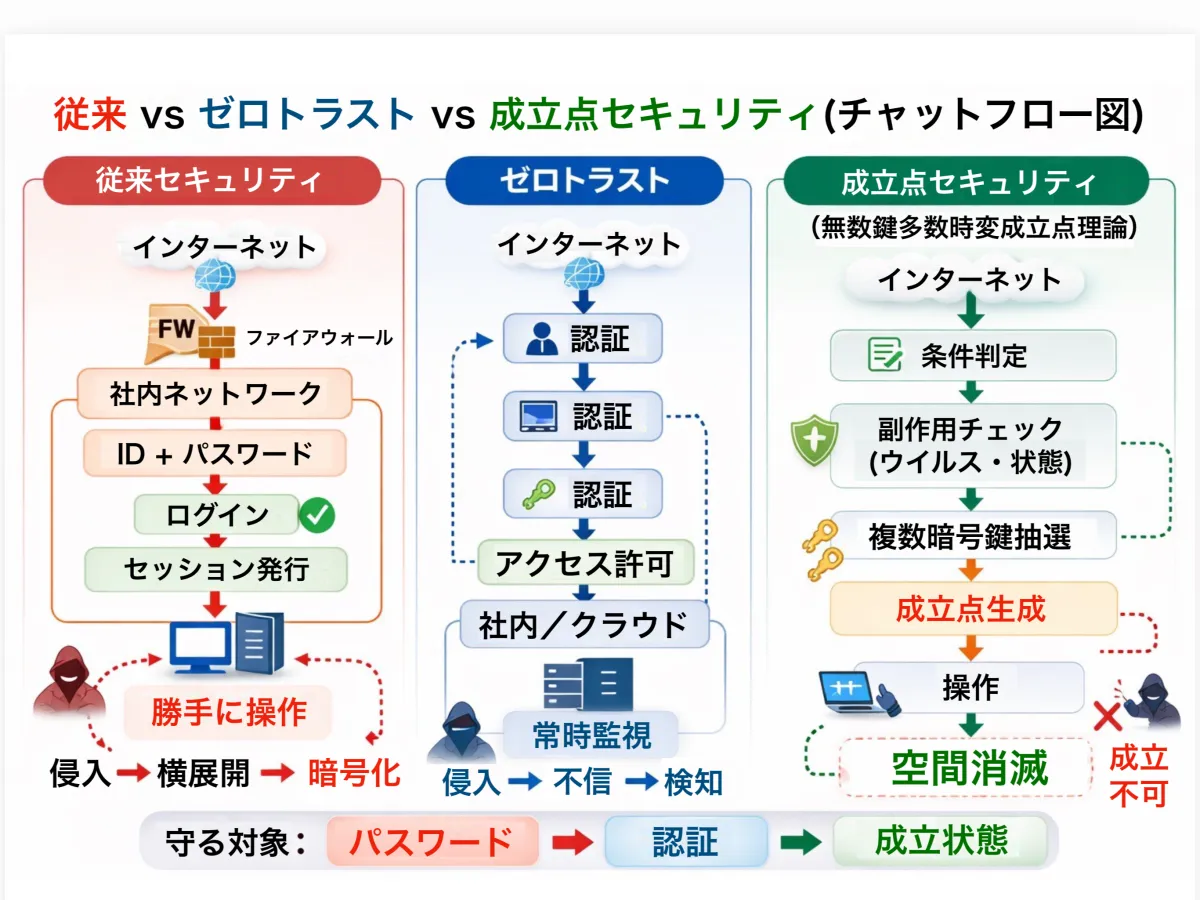
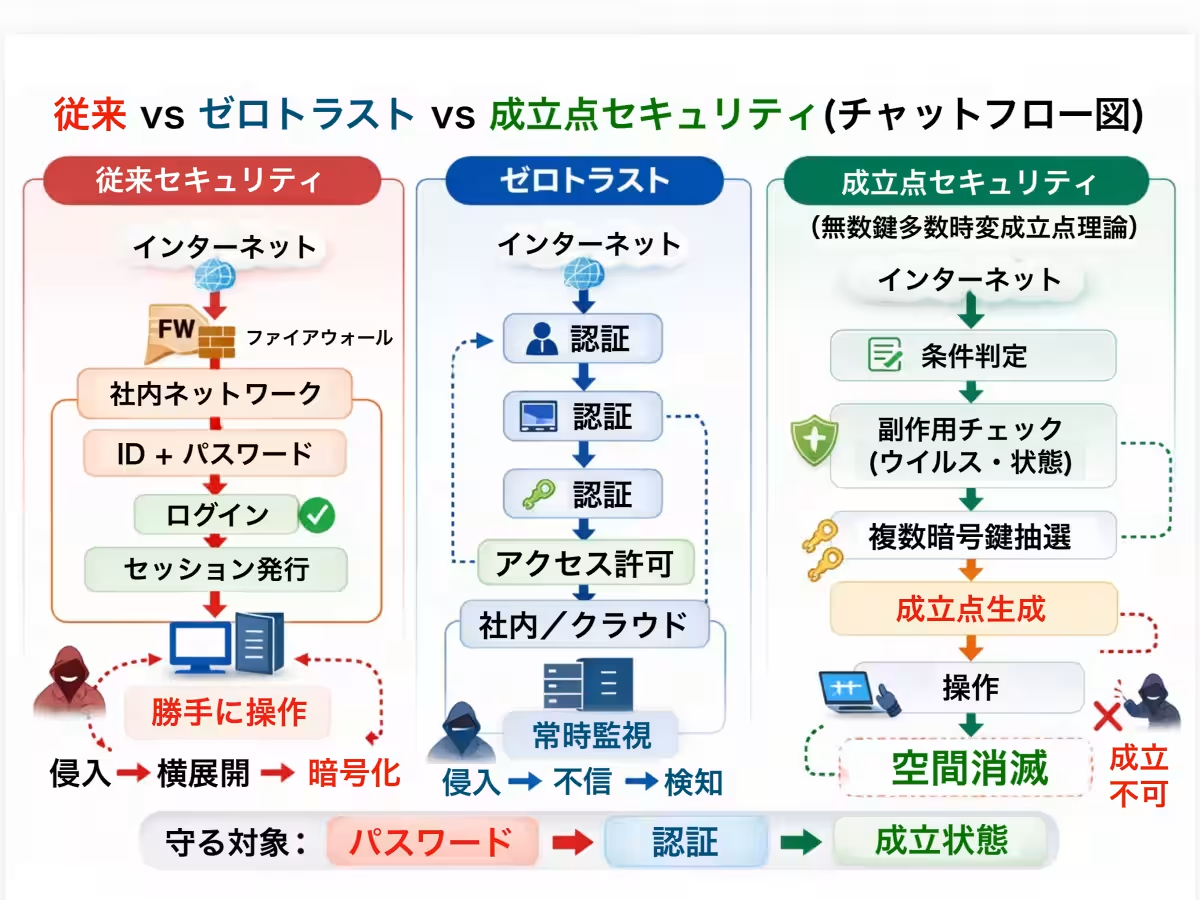
Historically, security systems were constructed to safeguard fixed data such as passwords and IDs. Examples of these conventional measures include:
- - IDs
- - Passwords
- - Fixed Tokens
- - Static Sessions
Such structures make security highly vulnerable to breaches, leading to issues such as data leaks, reuse of credentials, lateral movement across systems, and AI-driven attacks. Attacks often build upon one another, exploiting predictable and fixed security measures.
A New Perspective
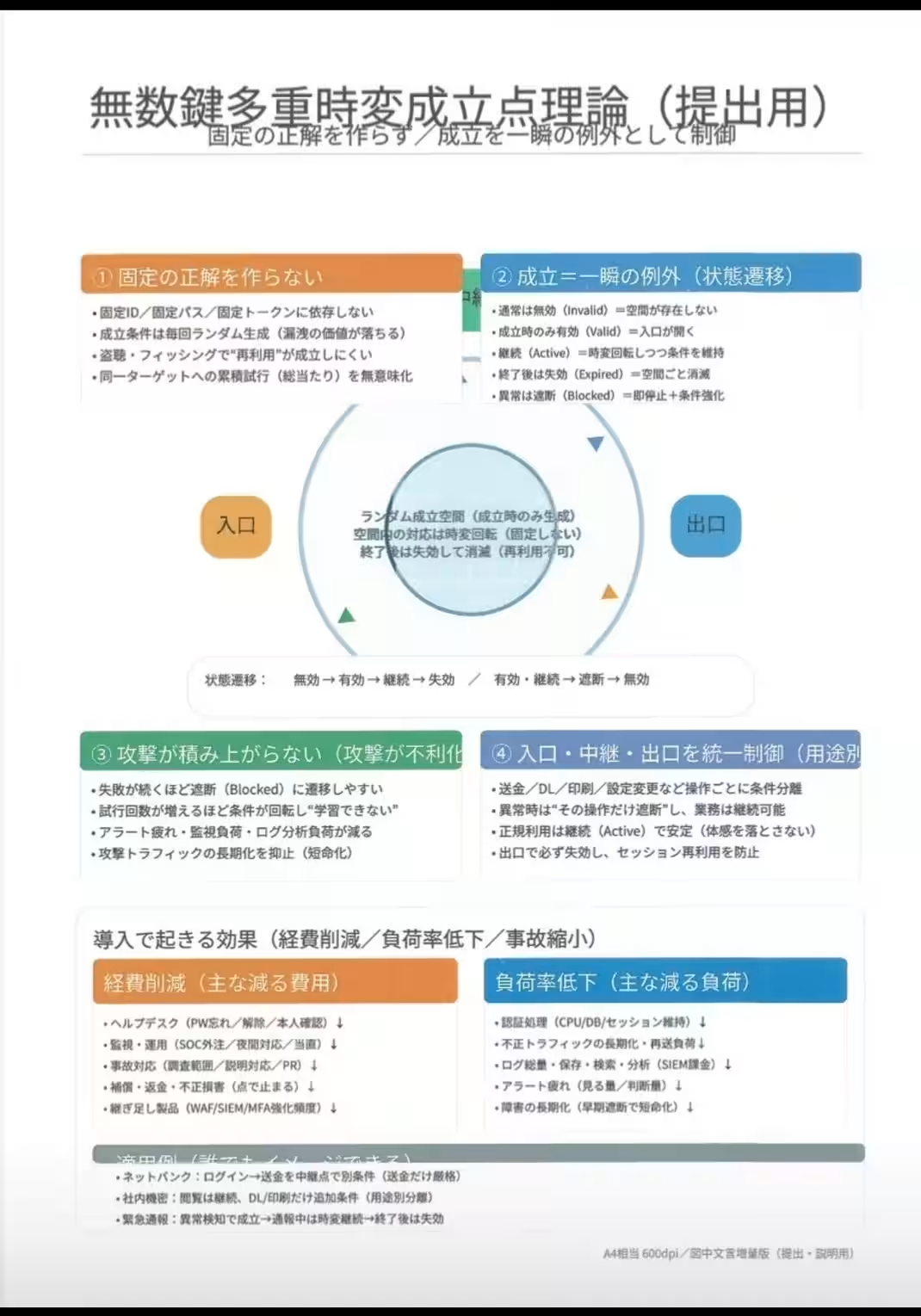
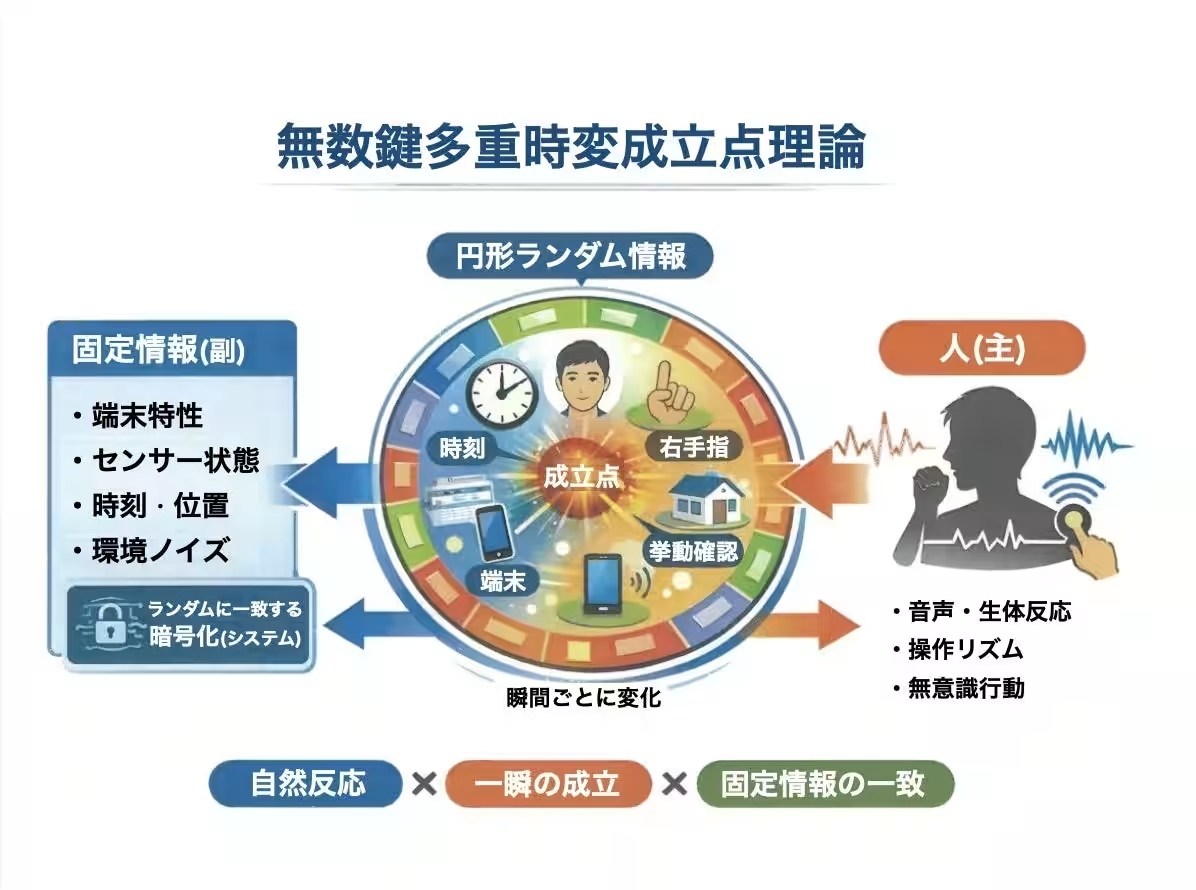
The Theory of Infinite Keys represents a paradigm shift in security design. Instead of safeguarding secret information, it focuses on the state of validation itself. Key aspects of this theory include:
- - Validation occurring as a brief anomaly
- - Random space generation for each access
- - Space obliteration post-validation
- - The ability to validate even when a state is unachieved
This means the protection is not on the secret itself but on controlling the act of achieving that state. This theory is fundamentally opposite to traditional security measures.
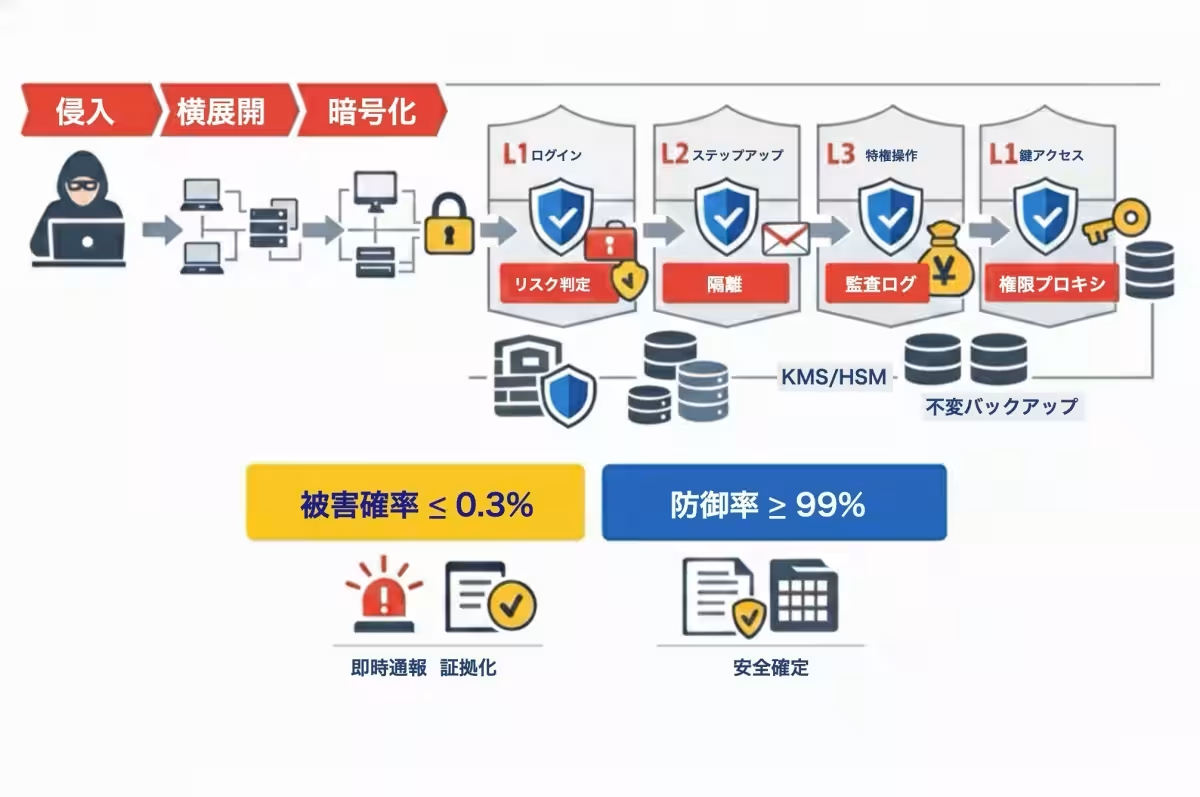
Unified Control Over Entry, Relay, and Exit
The gist of the theory integrates control over three essential points of interaction:
- - Entry (Login)
- - Relay (Operation)
- - Exit (Logout)
Unlike traditional systems that only reinforce entry points, this approach recognizes that many attacks occur within the relay phase, such as lateral movement or misuse of internal privileges. Therefore, the Infinite Keys theory surveils all aspects of interaction to ensure validation.
Forgetting Passwords is Ideal
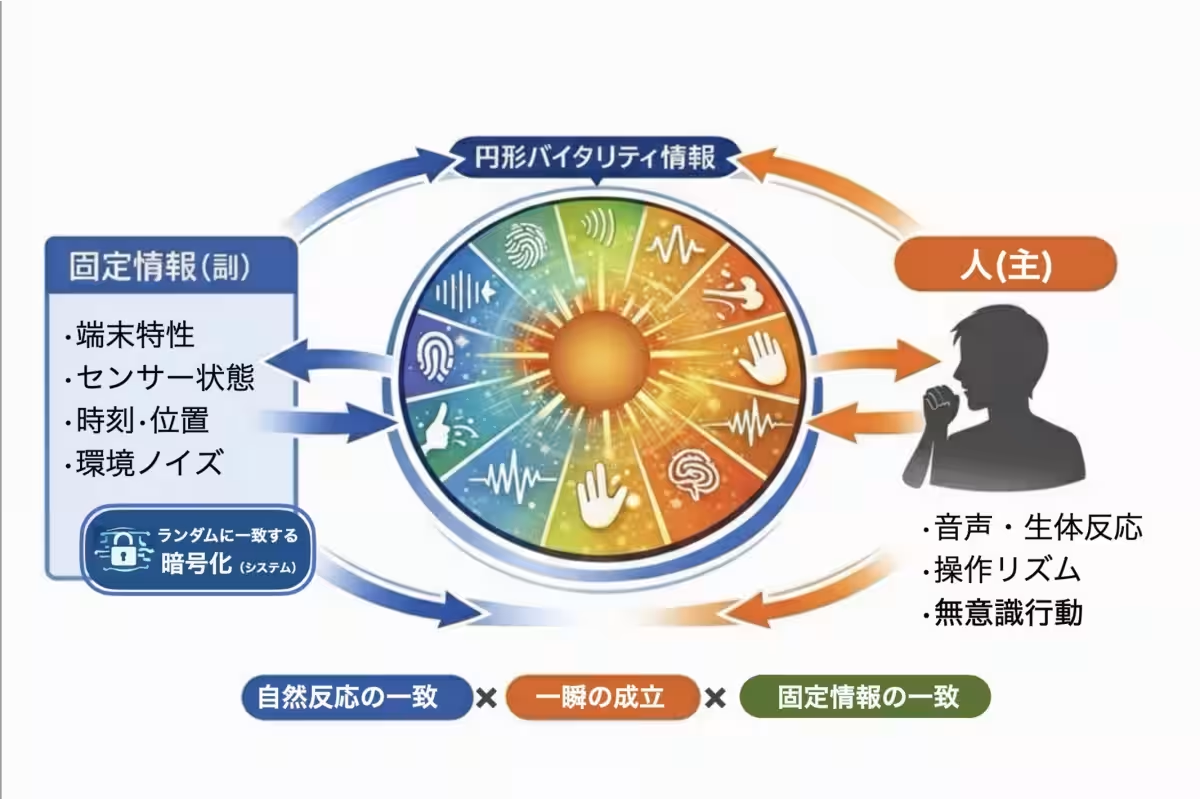
One of the revolutionary aspects of this theory is that it does not necessitate memorizing IDs or passwords. Instead, it relies on:
- - Human natural reactions
- - Operation rhythms
- - Environmental data
- - Device-specific details
- - Time stamps
This fosters a design where individuals do not need to remember secrets, allowing for a more secure arrangement.
Multi-Login Structure
Traditional models equate a single login with one session. In contrast, the Infinite Keys model permits multiple validations within a single login, such as:
- - Viewing Validation
- - Money Transfer Validation
- - Download Validation
- - Privileged Operation Validation
Each of these points uses different cryptographic keys selected through a randomized mechanism, thereby enhancing security exponentially.
The Structure of Infinite Keys
The theory derives its name from its core features of infinite keys, multiplicity, variability, and validation points. The key characteristics include:
- - Unfixed keys
- - Randomized selection
- - Temporal variability
- - Expiration upon validation
These attributes substantially hinder the likelihood of successful guessing, reuse, brute-force attempts, and AI learning, thus strengthening defenses. The design enables automatic checks for vulnerabilities using advanced AI techniques.
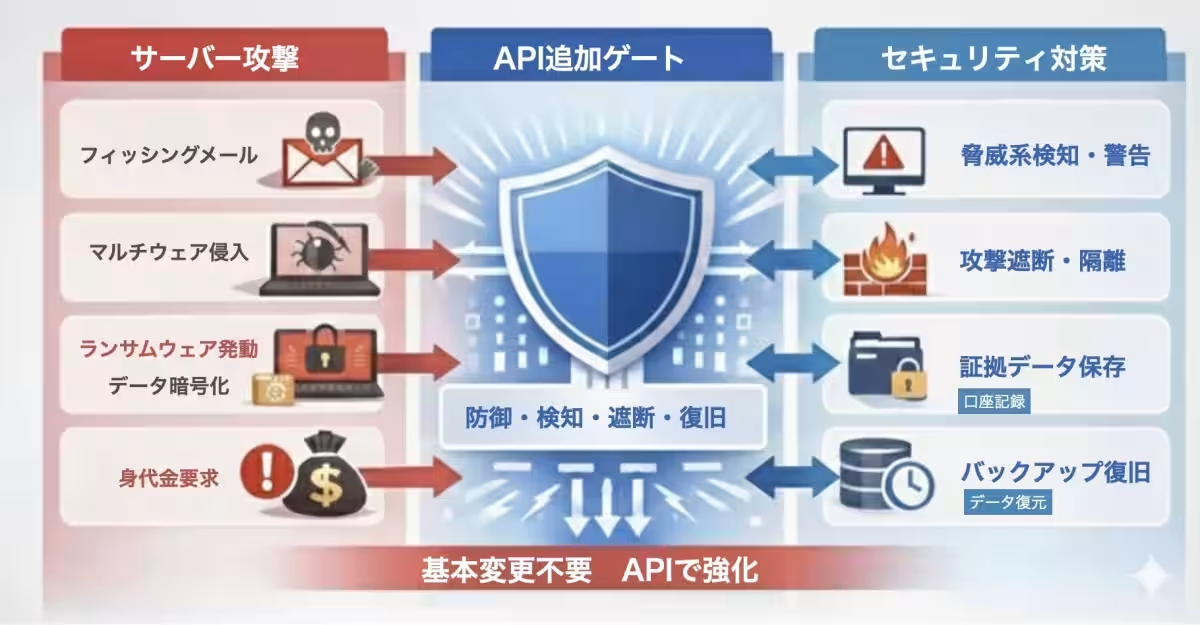
Comparison with 73 Attack Models
The Infinite Keys theory accounts for 73 different attack models—including phishing, deepfakes, and ransomware—comparing their mechanisms and allowing pre-validation for most attacks before they occur. This leads to a significantly more robust form of security, achievable at lower costs than traditional security developments.
Theoretical Design Metrics
The theoretical model asserts:
- - Defense Rate: Over 99%
- - Probability of Damage Occurrence: Below 0.3%
- - Improvement Rate: Exceeding several hundred million times
These metrics illustrate a strong potential for achieving robust security without necessitating foundational changes to existing systems.
Integrating with Other Technologies
Linking the Infinite Keys theory with existing patents in vital security and audio-based emergency alerts can enhance social safety. Potential applications may include detecting coercive crimes, preventing unauthorized transactions, preventing vehicle theft, and sending disaster notifications.
Social Implementation Possibilities
The scope for implementing this theory extends across multiple sectors including finance, governance, healthcare, corporate systems, and critical infrastructures. It employs a method that registers multiple cryptographic keys as audio signals, ensuring a randomized selection process.
Conclusion
The Theory of Infinite Keys and Variable States signifies a fundamental transition in security paradigms, shifting the focus from preserving static answers to controlling instantaneous states of verification. This innovative structure not only promises superior security but also offers vast potential for real-world applications across various industries.






Topics Other)










【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.