
Cyber Criminals Exploit AI as Vulnerabilities Surge by 43% in Q1 2026
Cyber Criminals Exploit AI as Vulnerabilities Surge by 43% in Q1 2026
In a startling revelation for the cybersecurity landscape, Beazley Security's latest Quarterly Threat Report has uncovered a dramatic 43% leap in exploited vulnerabilities during the first quarter of 2026. The report highlights the increasingly sophisticated tactics employed by cyber criminals, leveraging Artificial Intelligence (AI) to orchestrate more efficient attacks, particularly targeting supply chains and zero-day vulnerabilities.
Rising Vulnerabilities
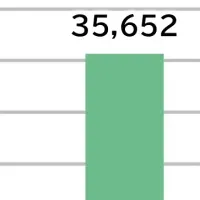
The report indicates that over 15,200 new vulnerabilities were disclosed in the first quarter, with approximately 3,900 categorized as high risk. This significant increase is marked by a 43% rise in the number of vulnerabilities listed in the Cybersecurity and Infrastructure Security Agency's (CISA) Known Exploited Vulnerabilities (KEV) catalog compared to the previous quarter. This acceleration signals a swift real-world weaponization of these vulnerabilities, posing escalating risks to organizations worldwide.
As organizations continue to grapple with these threats, Beazley Security Labs also reported a 15% increase in critical zero-day advisories issued to clients, underscoring the need for heightened vigilance in protective measures, notably for critical infrastructure components such as VPNs and firewalls.
March 2026: A Peak in Cyber Activity
Although the onset of the quarter experienced a seasonal lull in threat activity, March witnessed a surge in significant cyber incidents. In one such case, an autonomous AI agent undertook a wide-ranging scan of public code repositories, identifying and exploiting misconfigured access controls. This attack allowed a malicious group to compromise Trivy, a renowned vulnerability scanner relied upon in the software development community.
In another alarming incident, a hacktivist group linked to Iran executed a politically motivated attack against medical device manufacturer Stryker. Utilizing Microsoft Intune, they orchestrated a remote wipe on over 200,000 systems globally, showcasing the potential impact of cyber warfare tactics.
Targeting Developer Supply Chains with AI
A particularly noteworthy trend this quarter has been the rise of supply chain attacks that prioritize targeting non-human identities, as exemplified by TeamPCP. This threat actor utilized an automated AI tool dubbed "hackerbot-claw" to pinpoint and exploit misconfigurations within GitHub’s CI/CD workflows. The attackers managed to infect Trivy with credential-stealing malware, amplifying the compromise risk across countless downstream tools and organizations dependent on it, including popular projects like LiteLLM.
This alarming incident emphasizes a shift in tactics, where the emphasis is increasingly placed on the use of AI to breach security barriers within developer-centric pipelines.
Consistency in Ransomware Tactics
Ransomware incidents have remained steady this quarter, with a notable rebound in activity observed in March. The usage of compromised credentials continued to serve as the primary entry point for ransomware attacks, constituting 74% of recorded intrusions by Beazley's security teams.
Furthermore, security responders have noted a troubling rise in extortion-focused attacks where attackers exfiltrate data without deploying encryption. This lower-effort strategy provides attackers negotiation leverage against their targets while avoiding more complex ransomware deployment.
Insights from Beazley Security
Alton Kizziah, CEO of Beazley Security, remarked, "The first quarter began quietly but concluded with some of the most impactful cyber events we've encountered. What stood out was not just the sheer volume of cyber activity but also the impressive efficiency demonstrated by cybercriminals capitalizing on AI tools. Their ability to implement familiar tactics at an accelerated pace poses a significant challenge for security professionals."
Josh Carolan, director of security research at Beazley, added, "Rather than reinventing their operational playbooks, attackers are refining their methods, using AI-driven automation to expedite their efforts and increase their impact."
Conclusion
The findings from Beazley Security's Quarterly Threat Report reinforce the necessity for organizations to bolster their cybersecurity measures amidst an evolving threat landscape fueled by AI advancements. With many businesses still recovering from the profound impacts of previous attacks, vigilance and adaptability will be crucial in navigating the persistent challenges posed by cyber criminals in the coming months.
For a detailed overview, you can access the full Q1 2026 Quarterly Threat Report here.
Topics Other)





【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.