
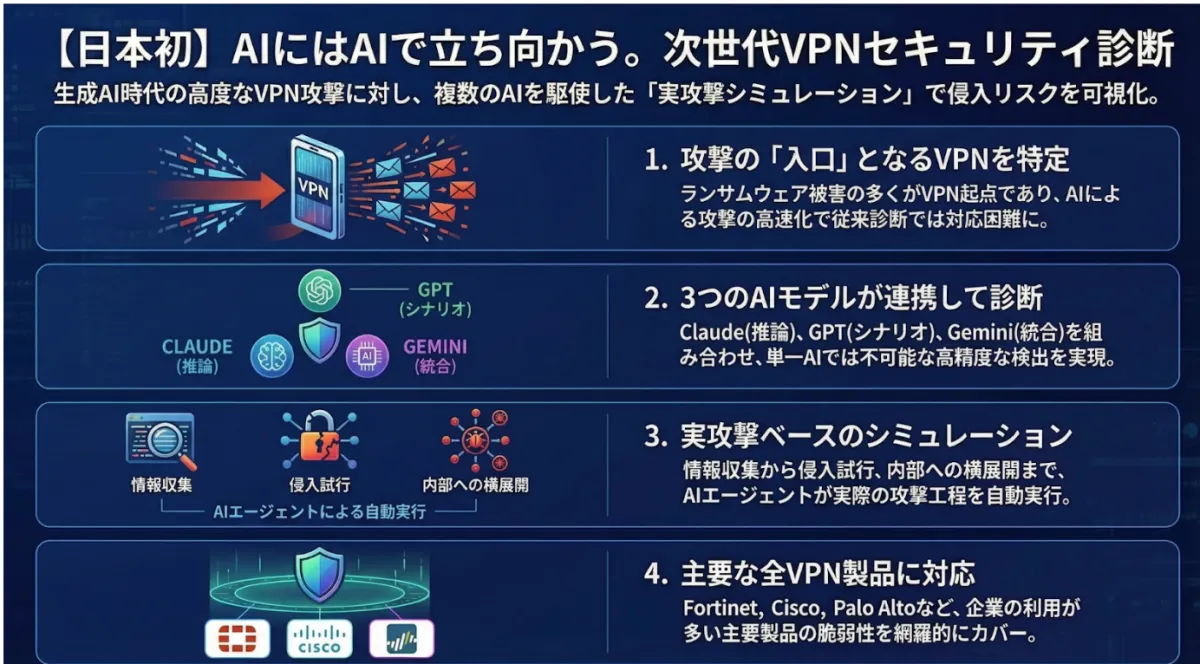
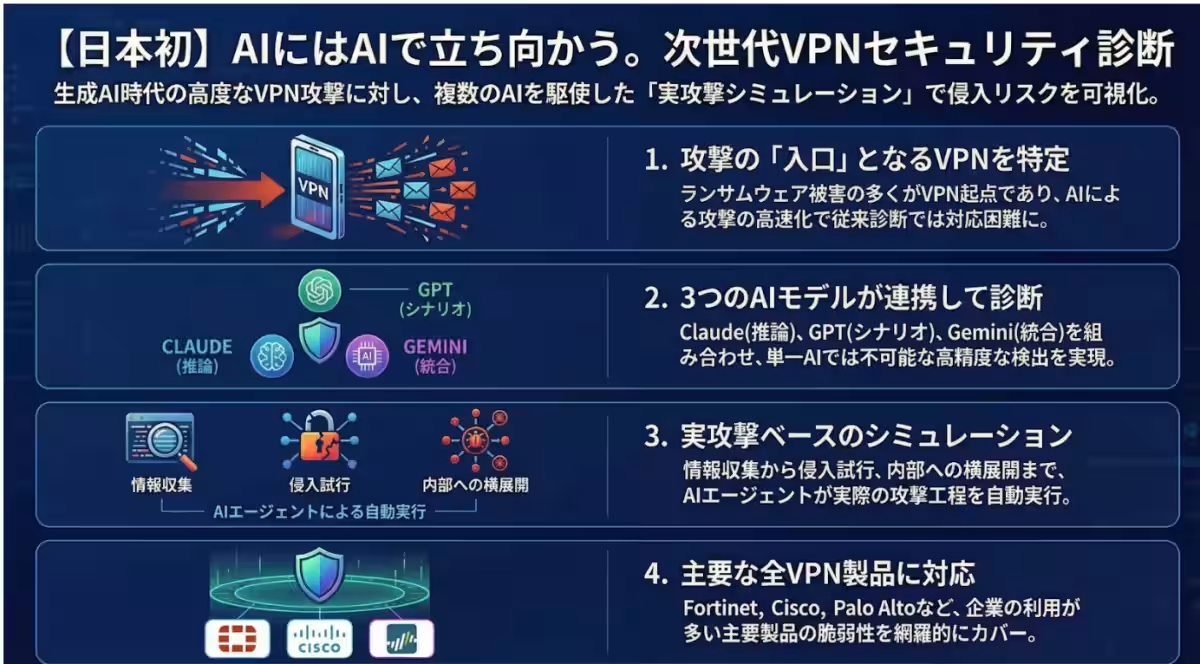
Powder Keg Technologies Launches AI-Driven VPN Security Diagnostic Service to Combat Cyber Attacks
Introduction
In a significant move for cyber security in Japan, Powder Keg Technologies has launched its latest offering: the AI-Driven VPN Security Diagnostic Service. This service leverages the power of advanced AI models to simulate cyber attacks on Virtual Private Network (VPN) devices, aiming to assist businesses in evaluating their risk exposure to potential network intrusions based on real attack scenarios.
The Context of Cyber Attacks and AI
Cyber attacks are evolving rapidly, especially with the emergence of Generative AI. Traditional security measures are increasingly inadequate, as the methods employed by cybercriminals have become more sophisticated. The automation of vulnerability discovery and the optimization of attack scenarios have dramatically increased both the speed and precision of these attacks. VPN devices serve as legitimate entry points into corporate networks, and once breached, they can expose the entire internal network to corporate espionage or data theft.
Recent studies indicate that a significant percentage of ransomware attacks originate from VPN vulnerabilities, with a concurrent increase in related Common Vulnerabilities and Exposures (CVEs). To navigate these ever-growing threats, there is an urgent demand for security approaches that utilize AI to assess and respond to vulnerabilities effectively.
Features of the AI-Driven VPN Security Diagnostic Service
1. Specialized VPN Risk Assessment
This service specifically targets VPN devices, effectively evaluating the intrusion risks associated with them. Some supported products include popular VPN solutions such as Fortinet FortiGate, Cisco AnyConnect, Palo Alto GlobalProtect, and Microsoft Azure VPN Gateway.
2. Multi-AI Agent Diagnostics
By combining multiple generative AI models, the service provides comprehensive diagnostics. Each AI fulfills distinct roles:
- Claude: Infers vulnerabilities and generates exploits.
- GPT: Develops attacking scenarios.
- Gemini: Integrates diagnostics and cross-checks results, effectively identifying risks that a single AI might overlook.
3. Real Attack Simulations
The service uses AI agents to automate the attack phases, which include:
- Information gathering
- Vulnerability inference
- Exploit code generation
- Attempted intrusions
- Lateral movement testing
This thorough simulation allows for visualization of potential intrusions, privilege escalations, and internal network compromises, offering companies vital insights into their security posture.
Offered Plans
- - STANDARD
- CVE scans
- AI attack simulations
- Dark web credential investigation
- Exploit testing
- - ADVANCE
- Lateral movement assessments
- Privilege escalation testing
- Active Directory attacks
- Data exfiltration evaluation
Strengths of Powder Keg Technologies
- - Domestic Security Products
- - World-Class Research
Future Aspirations
As generative AI continues to permeate cyber landscapes, further advancements in attack methodologies are anticipated. Powder Keg Technologies is committed to ongoing research and development of next-generation security technologies, ensuring that businesses can leverage digital environments safely.
For more information about their services and to see how they can protect your business, visit Powder Keg Technologies.
Topics Other)







【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.