Check Point's Lakera Sounds Alarm on Claude Code Configuration File Leak Risks
Rising Cybersecurity Risks with Claude Code's Configuration Files
In an alarming revelation, Lakera, an AI-native security platform under Check Point Software Technologies, has identified critical security risks associated with the configuration files generated by Claude Code, an AI coding assistant developed by Anthropic. The risk of credential exposure arises when these configuration files are inadvertently included in public npm package releases, potentially compromising sensitive information.
The Discovery of Exposed Credentials
Lakera's comprehensive scan revealed that approximately 1 in 13 of the checked configuration files contained sensitive data. The files, particularly the `.claude/settings.local.json`, can store various types of credentials such as API keys, authentication tokens, and other sensitive information that, when exposed, could lead to unauthorized access to accounts or services.
Background on Claude Code
Claude Code operates as a terminal-based AI agent that assists users in coding projects. One of its functionalities allows it to save approved shell commands in local configuration files. Should a project be made available as an npm package, there's a considerable risk of exposing these files to public view, thus jeopardizing user credentials.
Inspiration for this investigation was drawn from a post by Kirill Efimov, who highlighted the presence of `.claude/settings.local.json` in public npm packages. Lakera's team then developed a TypeScript service to monitor the changes in npm's CouchDB that would help track both new and updated packages, ensuring they could identify and analyze those containing `.claude` settings.
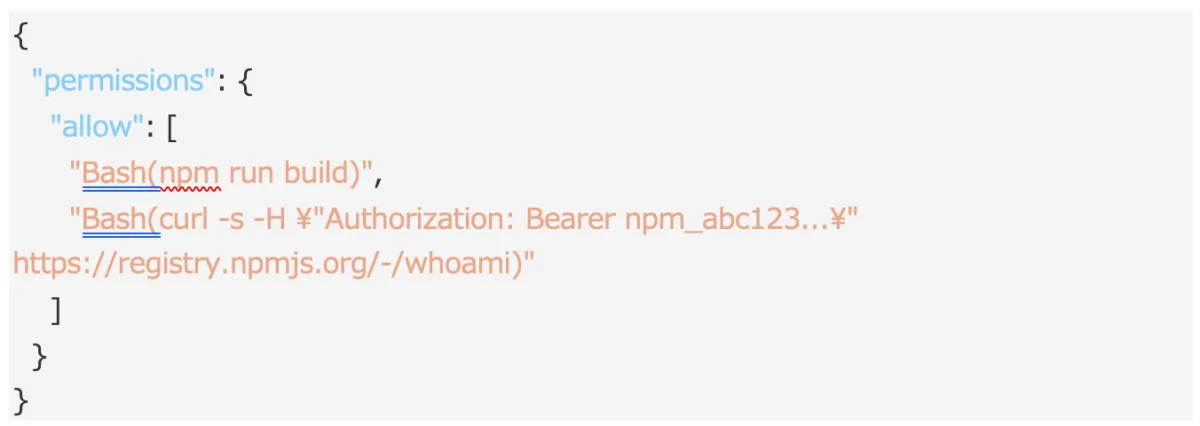
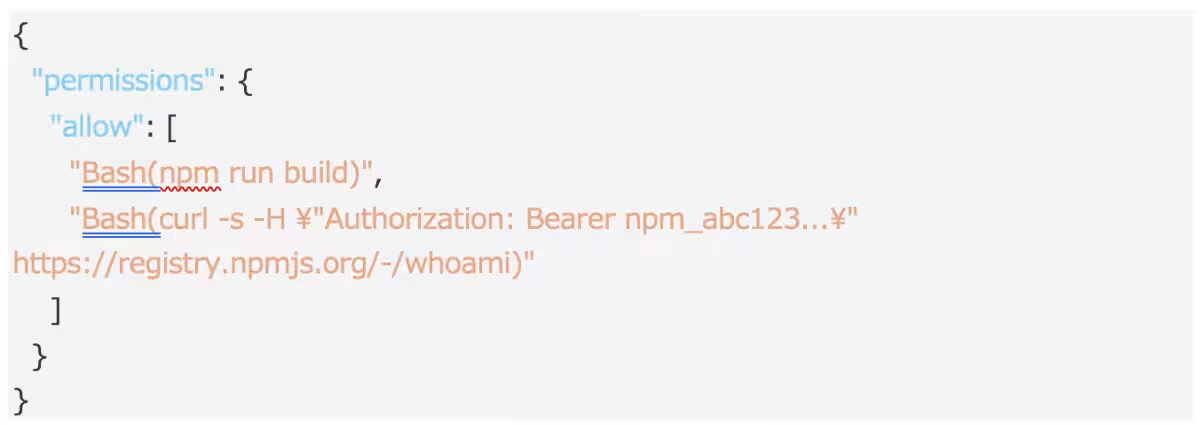
Understanding Claude Code’s Permission Model
Claude Code features a permissions system that deals with shell commands. If the AI attempts to run an unauthorized command, it offers users options including an 'allow always' choice. This selection leads to the command being written permanently into the `.claude/settings.local.json` file as an authorized entry, effectively making it so that future runs of the command do not require user approval.
This setup not only saves the command but also any associated credentials, such as API keys or authorization headers, creating a potentially harmful accumulation of sensitive information over time.
The Gap in npm Package Publishing
The procedure for generating npm packages can inadvertently allow sensitive files, like `.claude/settings.local.json`, to be published. Although files can be excluded via `.npmignore` or the `files` field in `package.json`, no default exclusions are set for `.claude/`, which means developers may encounter no warnings during the publishing process. As hidden dot files, `.claude/settings.local.json` easily goes unnoticed in normal workflows, increasing the risk of exposure.
In the scanning period, Lakera identified the `.claude/settings.local.json` across 428 out of approximately 46,500 packages, confirming that 33 files contained credentials across 30 packages. Disturbingly, this translates to a significant 1 in 13 rate of sensitive data embedded in publicly accessible configuration files.
Types of Credentials Found
The investigation unveiled various forms of sensitive credentials embedded within the files, including:
- - npm authentication tokens used for package publishing.
- - Plaintext login credentials (username, password, email address).
- - GitHub personal access tokens (both fine-grained and classic).
- - Telegram Bot API tokens enabling full control over relevant bots.
- - Bearer tokens for third-party services.
- - Hugging Face API tokens.
- - Plaintext credentials intended for local development scripting, usually embedded in curl commands.
Why These Files are Easily Overlooked
One of the inherent dangers of these configuration files is that, at first glance, they do not appear to contain sensitive information. They merely present as lists of shell commands, often leading developers to overlook their impact during the public workflow.
As developers frequently approve commands within Claude Code, it can escalate the risk when users choose 'allow always' for commands involving sensitive requests, effectively storing this information permanently within the file.
Recommended Preventive Measures
To mitigate risks associated with exposing sensitive information, the following steps are advised:
1. Exclude the `.claude/` directory from public exposure: Modify your `.npmignore` and add `.claude/`. If controlling via the `files` field in `package.json`, double-check before publishing.
2. Avoid including `.claude/settings.local.json` in version control: Make sure your versioning system ignores this file.
3. Review published package content closely: Utilize the command `npm pack --dry-run` prior to publishing.
4. Audit previously published versions: Check if already published versions contain the sensitive configurations with `npm pack
Once a file is published, the npm tarball remains unchanged even if the version is deprecated. Therefore, any credentials exposed at the time of publication are compromised, regardless of their subsequent discovery.
Rotating npm tokens and other credential types as necessary provides an essential safeguard against potential misuse stemming from earlier exposures.
Conclusion
While the `.claude/settings.local.json` file is not inherently dangerous, the accumulation of sensitive information within it poses considerable risks. Existing default settings do not adequately protect against sensitive data being published with packages. Developers must prioritize adding this directory to their `.npmignore` files, thus ensuring that sensitive credentials do not inadvertently become public.
This article has been adapted from a blog post published on April 22, 2026, US time.
Topics Consumer Technology)




【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.