
Check Point Research Reveals Alarming Trends in Ransomware Activities for Q1 2026
Check Point Research Ransomware Report Q1 2026
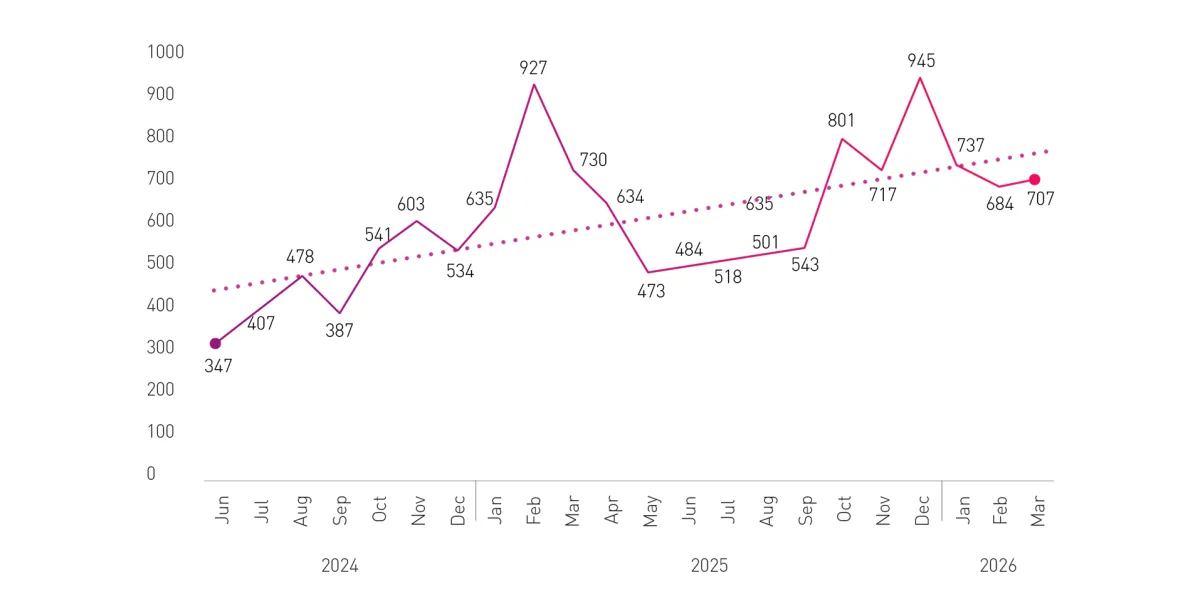
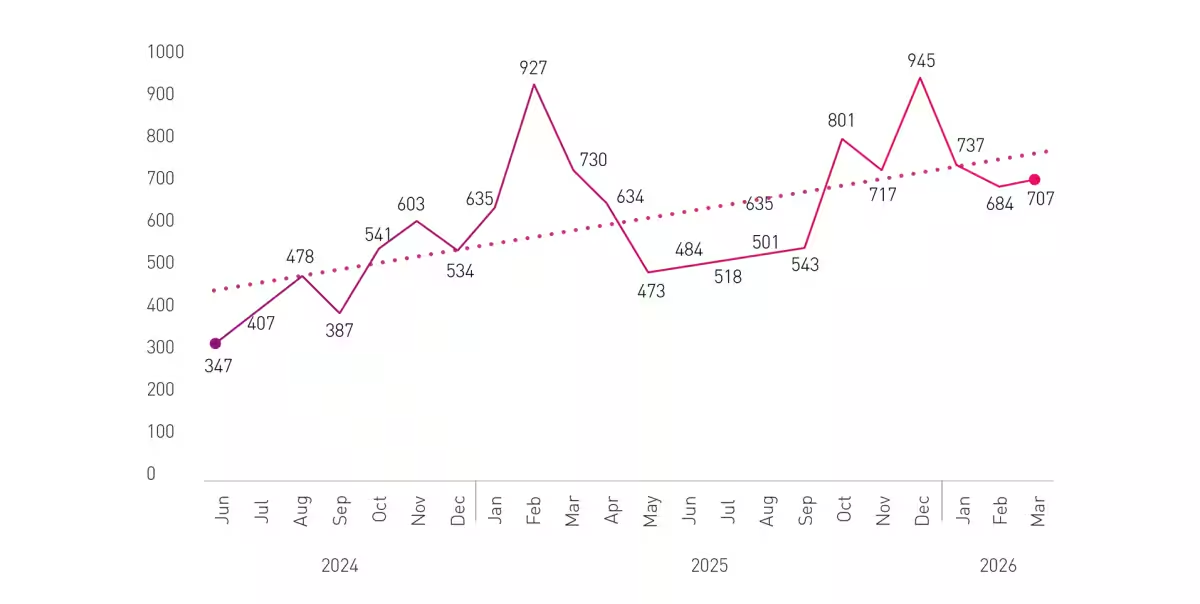
Check Point Software Technologies, a leader in cybersecurity solutions, has published significant findings regarding ransomware activities for the first quarter of 2026 through its division, Check Point Research (CPR). The report paints a dire picture of the current cybersecurity landscape, revealing that ransomware incidents remain alarmingly high, continuing a trend from the previous year.
Ransomware threats are no longer seen as sporadic spikes; rather, they have become a persistent danger for organizations worldwide. With records indicating that the number of organizations impacted has reached a staggering figure, cybersecurity professionals must be vigilant and enhance their defense mechanisms to combat these constant attacks.
Key Findings of Q1 2026 Report
1. Over 2,100 organizations targeted: In total, 2,122 organizations fell victim to ransomware attacks, marking the second highest number for a first quarter. This steady level of activity indicates that ransomware is an enduring threat that requires ongoing vigilance from businesses.
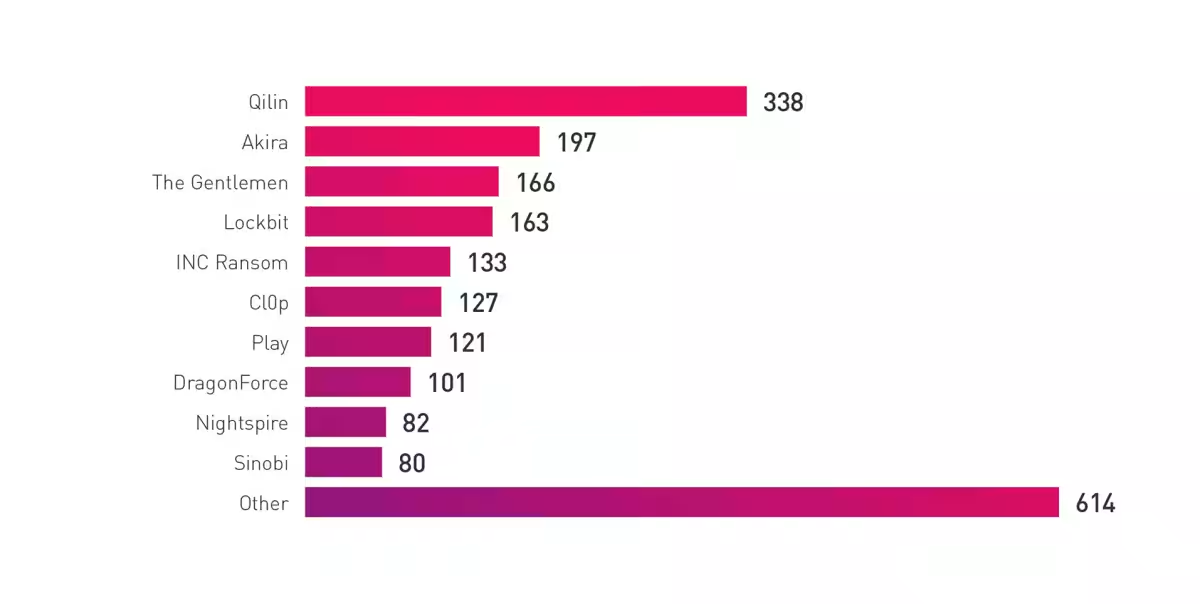
2. Dominance of top groups: A striking change has occurred compared to the prior year, with the top 10 ransomware groups now responsible for an astounding 71% of all reported attacks. This consolidation highlights the emergence of a select few groups that execute the majority of attacks with increasing efficiency and specialization, which only amplifies the risk of devastating impacts on compromised organizations.
3. Qilin leads with a significant presence: For the third consecutive quarter, the Qilin group has maintained its position as the most active ransomware entity, associated with 338 reported incidents. Meanwhile, The Gentlemen group exhibited exponential growth, escalating from just 40 attacks in Q4 2025 to 166 incidents in Q1 2026—a 315% increase, making it the fastest-growing group in recent months.
4. LockBit's resurgence: Following previous disruptions due to law enforcement actions, LockBit has reemerged as a key player in the global ransomware landscape, involved in 163 attacks in the quarter. This illustrates that while law enforcement may slow down operations, it rarely eliminates established groups entirely.
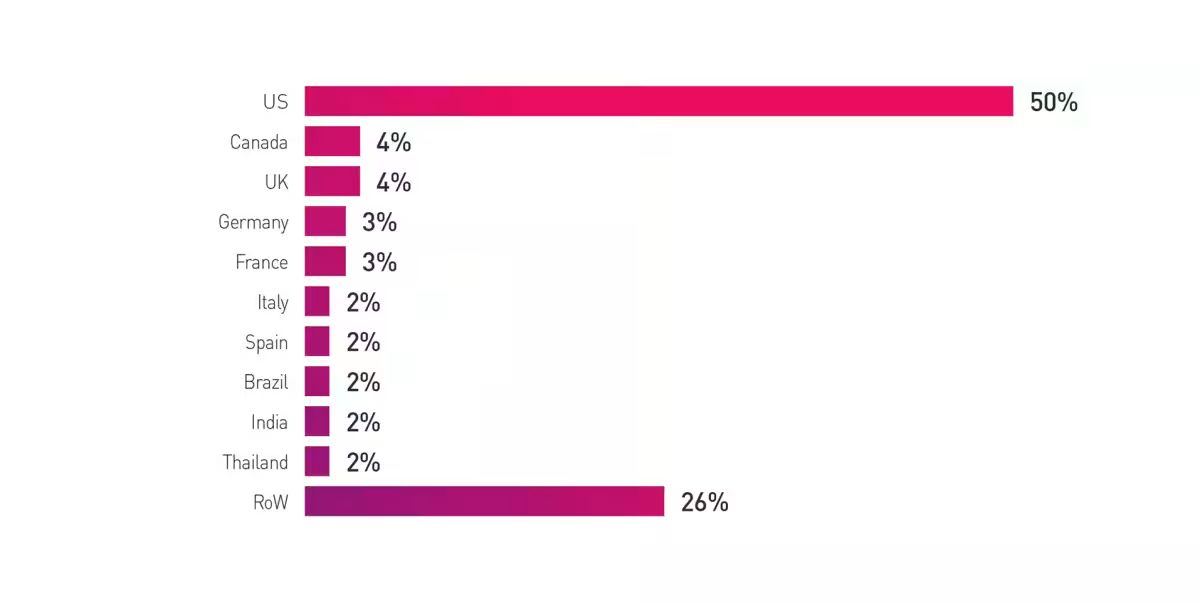
5. Geography of attacks: An inconceivable 49.6% of the world’s ransomware victims are located in the United States, affirming its status as a prime target for cybercriminals. Regions and industries give way to varying degrees of vulnerability, clearly suggesting that attackers prioritize targets based on access viability over traditional assessments of profitability.
The Strategic Shift in Targeting
An important observation gained from CPR's research indicates that ransomware attacks are increasingly directed at organizations deemed accessible rather than merely lucrative, thereby transforming the landscape of acceptable targets. Even industries not previously identified as high-yield are at risk if they exhibit unaddressed vulnerabilities or a weak infrastructure.
In these changing dynamics, critical sectors such as manufacturing, business services, healthcare, and industry continue to remain prime targets. Attackers thrive not on high-dollar ransom demands alone, but on the ability to create operational downtime and disruptions, making such interruptions their most effective strategy.
Conclusion
Sergey Shykevich, Threat Intelligence Group Manager at Check Point, emphasizes the urgency for organizations to shift their strategy from reactive measures to proactive defenses.
Topics Other)










【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.