
Chinese APT Actor 'Camaro Dragon' Initiates Attacks Amid Rising Tensions in the Middle East
Rising Threats from 'Camaro Dragon' in the Middle East
Recent geopolitical tensions in the Middle East have caught the attention of cybersecurity experts, particularly the threat intelligence division of Check Point Software Technologies, known as Check Point Research (CPR). Their latest report highlights a concerning uptick in activities by the Chinese APT actor dubbed 'Camaro Dragon', which has been actively targeting organizations in Qatar. This increase coincides with the intensification of conflict in the region, particularly following the commencement of the U.S. operation, 'Epic Fury', which set the stage for heightened cyber threats. One day later, on March 1, 2026, an observed attack campaign aimed at organizations in Qatar was initiated, drawing on propaganda related to missile attacks on Bahrain.
Attack Trends and Methodologies
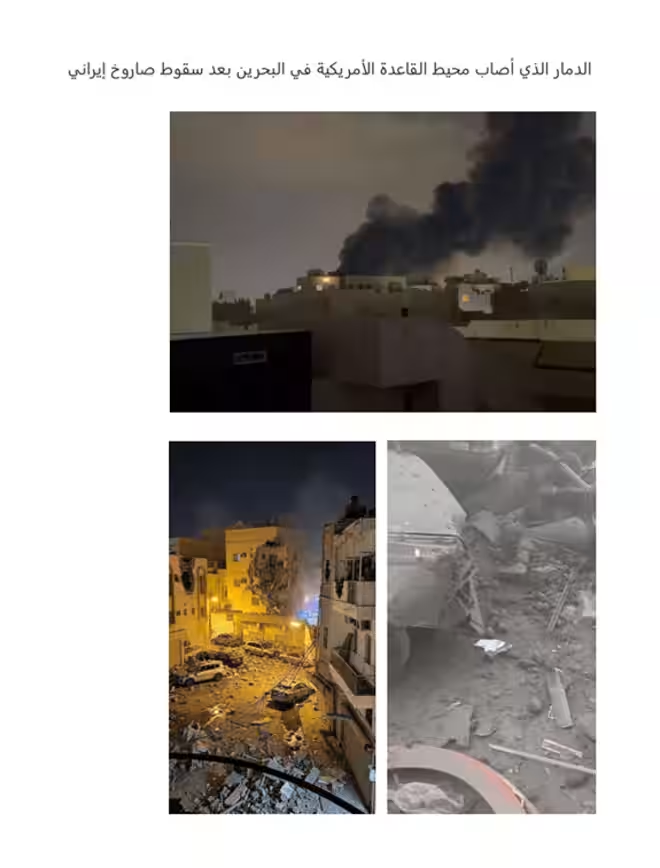
The recent activities of Camaro Dragon reveal a troubling adaptability to geopolitical developments, showcasing the ability of this APT actor to swiftly modify its attack tactics based on recent news and critical changes in the region. For example, the actor deployed a variant of PlugX malware as part of its campaigns, illustrating a preference for easily accessible and effective tools designed for rapid initial deployments.
The identified infection chain starts with an archive file disguised as a set of attack photos against a U.S. military base in Bahrain. Once an associated LNK file is executed, a complex infection chain is triggered, connecting to compromised servers to fetch subsequent payloads. Ultimately, this leads to a DLL hijack of legitimate binaries on Baidu NetDisk, which facilitates the deployment of the PlugX backdoor. This sophisticated backdoor has been used by various Chinese threat actors since at least 2008, showcasing a wide array of functionalities post-infection, including remote access, file exfiltration, screen capturing, and command execution.
A Broadening Focus
Interestingly, this method was not exclusive to the Qatar attack; CPR noted similar tactics being utilized against Turkish military targets months prior, suggesting that Camaro Dragon maintains a consistent targeting strategy across the broader Middle East. As the situation evolves, the group's operational focus seems to be shifting towards Qatar, reflecting the emergence of new targeting opportunities stemming from the evolving geopolitical landscape.
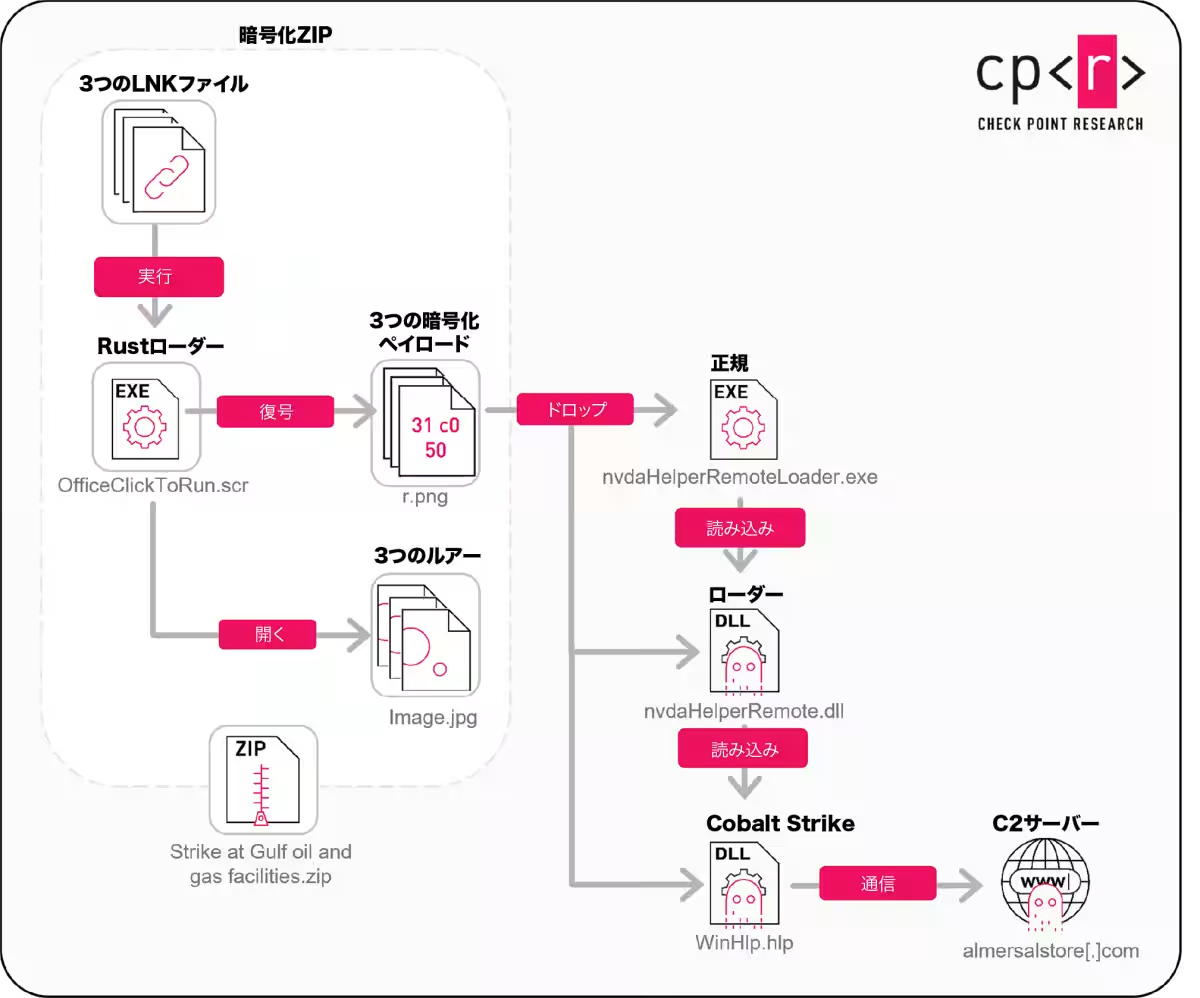
In a different attack campaign focused on Gulf oil and gas facilities, another password-protected archive named 'Strike at Gulf oil and gas facilities.zip' was identified. This campaign employed AI-generated bait masquerading as the Israeli government to deploy a Rust-based loader, previously unseen in such contexts. The loader exploited a DLL hijack of the NVDA component from the open-source screen reader NVDA, a tactic seen rarely associated with previous Chinese campaigns.
Subsequently, the final payload in this campaign was identified as Cobalt Strike, often repurposed for malicious activities despite being initially designed as a penetration testing tool. This underscores the actor’s tendency to deploy it in initial stages to conduct reconnaissance on newly compromised systems, further assessing whether to escalate their intrusion activities.
Implications of Shifting Priorities
What is particularly alarming is that the activities observed suggest a significant reorganization of priorities within Chinese-related threat actors in response to recent regional developments. While the Gulf region has not been prominently featured in previous discussions around Chinese cyber activities, the observed campaigns signal that as the geopolitical narrative shifts, so too does the focus of cyber espionage and threats. The rapid pivot to targeting key organizations in Qatar, utilizing conflict-related lures, highlights how promptly these actors can adapt their strategies based on the dynamic information landscape emerging from regional crises. This evolution could signify broader implications regarding intelligence collection priorities centered on states like Qatar, which lie at the intersection of multiple regional and global interests.
This analysis underscores the importance of vigilance in cybersecurity as geopolitical tensions morph rapidly, and APT actors like Camaro Dragon demonstrate their capability to capitalize on these shifts for malicious purposes.
Conclusion
The insights provided by Check Point Research offer a critical lens into the current landscape of cyber threats, particularly as they relate to Chinese state-affiliated groups like Camaro Dragon. By continuously evolving their tactics to align with global events, these APT actors remain a significant concern for nations and organizations alike in the ever-changing realm of cybersecurity. Keeping abreast of such developments is essential for maintaining robust defenses against the multifaceted nature of cyber warfare today.
- ---
Topics Other)










【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.