Beware of Deceptive Recruitment Schemes Targeting Job Seekers in the AI Era
Beware of Recruitment Scams in the Age of AI
As the digital landscape evolves, job seekers must remain vigilant against increasingly sophisticated recruitment scams. Recently, NordVPN, a prominent provider of personal security services based in Amsterdam, revealed the alarming findings of its Threat Intelligence Research Department regarding new deceptive practices that mimic the hiring processes of major global companies.
Overview of the Scam
The investigation has uncovered a new multi-layered approach to recruitment fraud, using emails impersonating hiring managers from reputable firms like Meta, Disney, Coca-Cola, and Spotify. Job seekers receive seemingly legitimate recruitment emails that lead them to fake job sites, designed to look just like the real ones. The ultimate goal? To compromise the victim's social media accounts, primarily Facebook.
Such tactics have been identified worldwide and their growing prevalence in Japan poses a significant risk to local job seekers.
Background of the Investigation
With the rise of generative AI and an increase in phishing scams, cyberattacks have evolved to effectively mimic legitimate companies. This complex form of attack includes convincingly replicated company websites, hiring information, and email communications, making it increasingly challenging for individuals to discern between authentic and fraudulent engagements. Especially those actively looking for jobs may find themselves vulnerable, as they are more likely to respond to unsolicited offers and let their guard down regarding personal data.
To shed light on this trending deception, NordVPN conducted thorough research within its Threat Intelligence division.
Research Details
Study Title: NordVPN Threat Intelligence Research Department
Research Institution: NordVPN, NordStellar
Date of Study: March 31, 2026
Methodology: Advanced search strings applied to major search engines and the use of IoT search engines like Fofa.io and Shodan.io to identify domains, services, and ports.
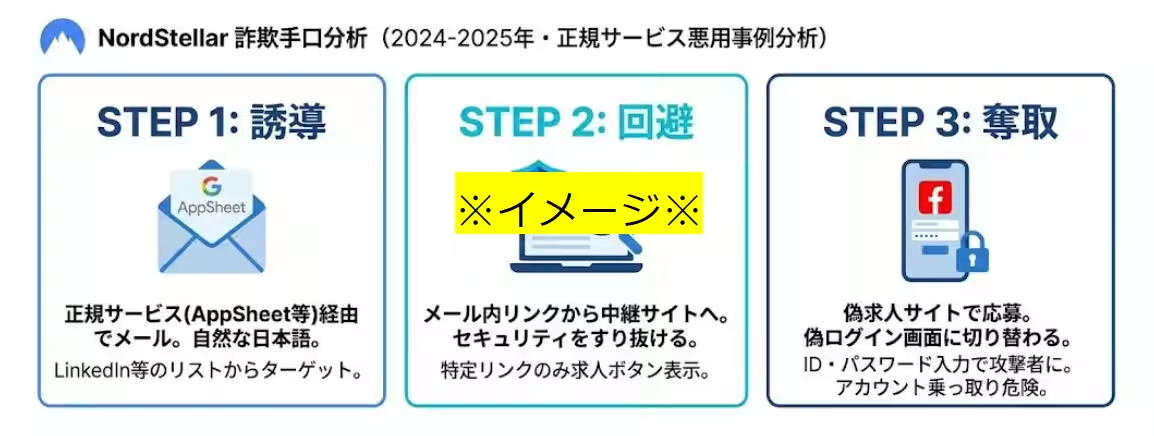
The Three-Stage Deceptive Process
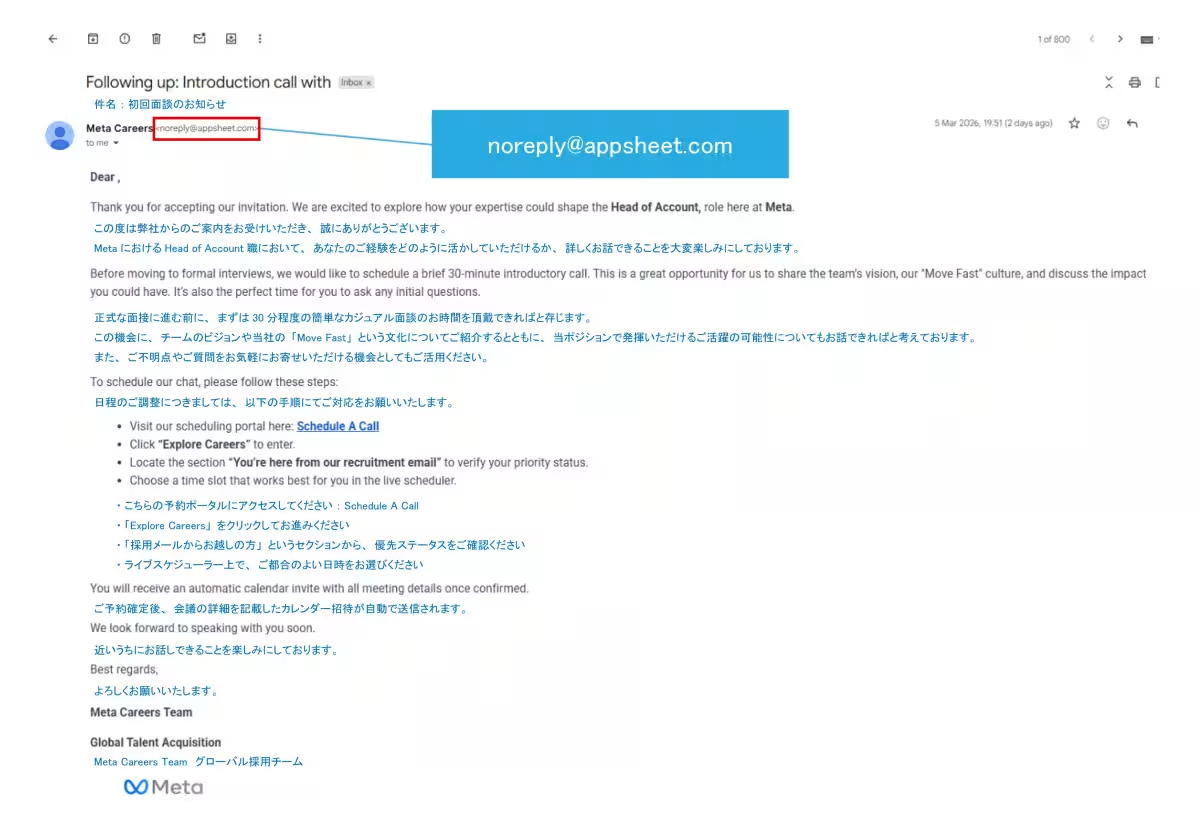
The fraud detected involves a clever three-step methodology that seamlessly lures victims without raising suspicion. The initial stage starts with a legitimate-looking recruitment email sent through Google AppSheet. These emails are written in fluent Japanese, closely resembling real recruitment communications. Because AppSheet is a legitimate service provided by Google, the sender's address appears as “appsheet.com,” making it less likely to be flagged as spam and preventing recipients from questioning its authenticity.
It is believed that the recipient lists are generated from platforms like LinkedIn or derived from past data breaches.
Upon clicking a link in the email, the victim is redirected to a proxy website, such as `careers.meta-findyourjob[.]com`. This site has intricate security features that evade detection; antivirus software and search engine crawlers only see benign pages. Only by clicking a specific link within the fraudulent email does the
Topics Other)




【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.