

Unveiling the Cyber Espionage Campaign 'Silver Dragon': A Deep Dive
Unveiling the Cyber Espionage Campaign 'Silver Dragon'
Recently, Check Point Research, a leading threat intelligence division of the globally renowned cybersecurity firm Check Point Software Technologies, disclosed alarming details regarding a cyber espionage operation named 'Silver Dragon'. Associated with the notorious APT41 group, this operation has adopted cunning strategies to conduct covert surveillance activities, extensively exploiting legitimate Windows services and utilizing Google Drive for command and control communications. Since emerging in mid-2024, Silver Dragon has primarily targeted government and public sectors within Southeast Asia and parts of Europe, emphasizing stealth and protracted data collection over destructive actions.
Targeted Regions and Methods
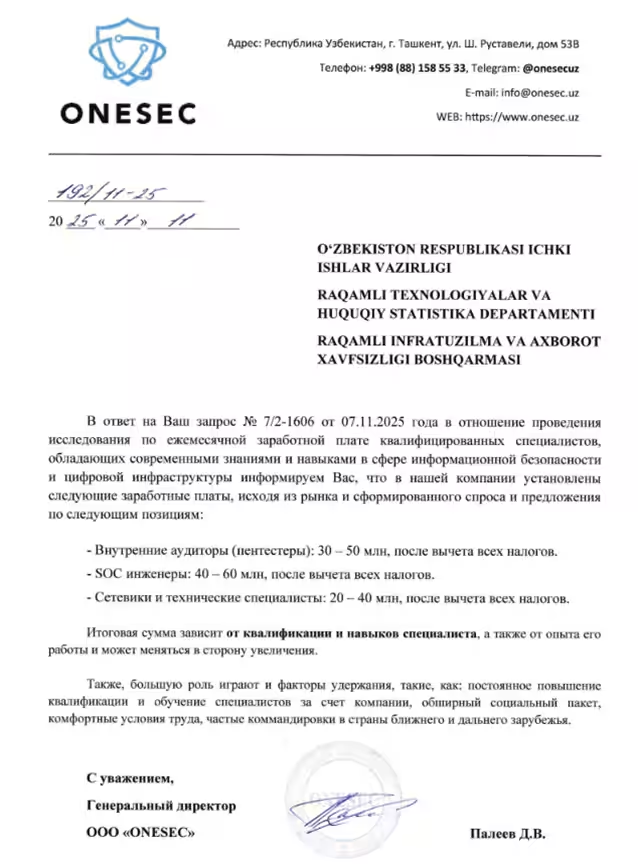
While the campaign predominantly attacks Southeast Asian entities, reports have confirmed victims in Europe and highlighted phishing endeavors aimed at Uzbekistani government agencies. This strategic focus underscores an acute aim for collecting vital state information.
Initial Access Techniques: The operation employs two primary methods for infiltration: the exploitation of publicly accessible servers and email phishing attacks. This dual-approach successfully compromises organizations that rely heavily on email and public infrastructures, greatly amplifying the attack surface of public institutions.
Unfortunately, many organizations remain vulnerable to these tactics, as displayed in a phishing email masquerading as an official document destined for an Uzbek governmental agency.
Innovative Stealth Techniques
Exploitation of Windows Services: Rather than overtly deploying malicious services, Silver Dragon cleverly hijacks established Windows services, including Windows Update, Bluetooth Update, .NET ClickOnce, and others to load malicious code discreetly. By blending malware operations into the usual system functions, it becomes vastly more challenging for organizations, especially large enterprises and agencies, to detect the anomaly.
Cloud-based Command and Control
At the heart of this sinister campaign lies a custom backdoor dubbed 'GearDoor', ingeniously utilizing Google Drive as a file-based C2 channel. Infected machines create specific cloud folders and leverage files that appear benign (like .png or .rar file disguises) to transmit encrypted commands and execution results. Given that Google Drive traffic is generally permitted and trusted, the malicious operations blend seamlessly into valid cloud activity, raising significant concerns regarding how defensive measures perceive ostensibly 'harmless' SaaS traffic.
Advanced Monitoring Capabilities
Moreover, Silver Dragon integrates a stealthy screen monitoring implant known as 'SilverScreen'. This tool captures screenshots only when meaningful changes occur on the screen, enabling long-term surveillance of users yet minimally impacting system operations. Consequently, the operation focuses not just on short-term access but ongoing intelligence gathering.
Leveraging Legitimate Tools and Frameworks
The ultimate payload to be deployed through multiple infection chains often manifests as a Cobalt Strike beacon, which communicates via DNS tunneling or HTTP, and may even utilize SMB communications within internal networks to mask malicious traffic further. The combination of custom loaders, legitimate OS components, and the use of widely exploited red teaming tools illustrates a high degree of sophistication typical of established and resource-rich espionage operations.
For cybersecurity defenders, Silver Dragon serves as a stark reminder that threats no longer strictly arise from overtly malicious infrastructures. Instead, critical OS services and trusted cloud platforms face covert exploitation, prolonging dwell times and circumventing traditional defensive measures.
Implications for Governance and Institutions
This signifies an intensifying necessity for enhanced endpoint visibility, service-level monitoring, and scrutiny of cloud traffic—an imperative particularly acute for governments and significant public institutions, notably amid ongoing geopolitical cyber pressures.
Sergey Shykevich, the Threat Intelligence Group Manager at Check Point, remarked, “Silver Dragon exemplifies the evolving nature of modern cyber espionage, with attackers leveraging multiple initial access means and embedding themselves within trusted platforms such as Windows and Google Drive. Our investigation underscores that cloud traffic and core OS components can no longer be considered fundamentally safe. Organizations, especially governmental ones, must prioritize rapid patching of public servers, robust email defenses, and continuous monitoring of authorized cloud activity to safeguard their environments.”
The study reveals that the future of cyber defense hinges on adopting a prevention-first approach while ensuring comprehensive visibility that can detect even the most insidious exploitation masquerading as routine operations.

Topics Other)







【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.