

Understanding the Destructive Cyber Attacks by Handala Hack Targeting Iran and Albania
Overview of Handala Hack's Activities
Check Point Research (CPR), the threat intelligence division of the global cybersecurity leader Check Point Software Technologies, has recently released findings regarding the Iranian-affiliated threat actor known as Handala Hack. This group has been expanding its operations amid escalating tensions in the Middle East, particularly focusing on destructive attacks that have implications for various geopolitical players.
Key Findings
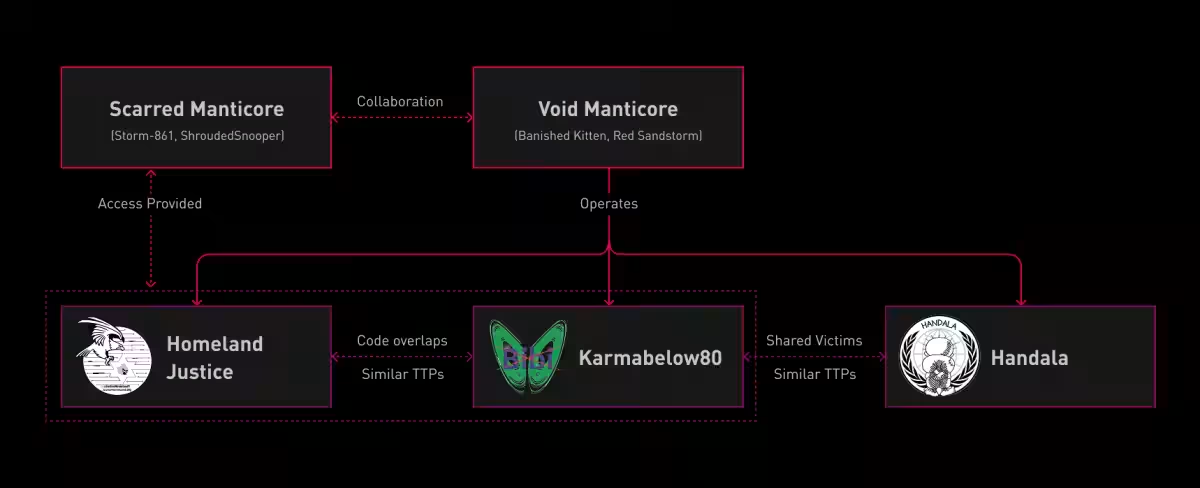
The Handala Hack is primarily associated with the Iranian Ministry of Intelligence and Security (MOIS) and operates under the online persona Void Manticore, otherwise known as Red Sandstorm or Banished Kitten. This actor utilizes various identities, including Karma and Homeland Justice, which have been linked to attacks targeting Israel and Albania.
Handala is known for executing data destruction attacks through traditional tactics, techniques, and procedures (TTPs), engaging in hands-on activities within victim environments and simultaneously conducting multiple data deletion attacks. Recent advancements have included the use of the NetBird platform for traffic tunneling within networks, and AI-assisted PowerShell scripts for executing data destruction.
Previous research by CPR has recognized Handala as a state-level threat actor notorious for its hack-and-leak tactics that involve data theft and subsequent exposure, especially targeting entities such as the large medical technology firm, Stryker, to expand its operational reach into the United States.
The TTPs associated with Void Manticore have shown little significant change from 2024 to the present, with an ongoing reliance on hands-on infiltration and readily available erasure and encryption tools, thus reiterating the importance of CPR's analyses conducted over the years in understanding these operations. The group utilizes both custom-developed tools and publicly available resources while leveraging underground criminal services for initial access and malware procurement.
In light of the evolving scope of operations undertaken by this group, CPR has compiled observations focused on their latest TTPs and newly identified indicators of compromise (IoCs). The predominantly hands-on nature of these activities suggests a tendency for such indications to be relatively short-lived, often consisting of commercial VPN services, open-source software, and commonly accessible offensive security tools.
Background of Handala Hack
The persona Handala Hack derives its name from a Palestinian cartoon character, and since late 2023 it has been recognized as one of three major operational aliases within the Void Manticore group. The other two identities are Karma and Homeland Justice, with the latter still engaged in operations targeting Albania. Findings from CPR illustrate that the compromise activities linked to these personas demonstrate similar TTPs, and there is overlap in the code deployed in wipe attacks. Karma and Homeland Justice have also shown connections to another Iranian threat actor, Scarred Manticore.
There are indications that Handala and Karma may have initially operated as separate operational units within the same organization and later consolidated into a single brand, allowing Handala to emerge as the principal external persona. Official resources suggest that Void Manticore is linked to the domestic security sector of the MOIS, particularly its counter-terrorism department.
Initial Access Tactics
Handala focuses on compromising IT companies and service providers to steal authentication credentials, primarily leveraging compromised VPN accounts for initial access. In recent months, there have been hundreds of instances of login attempts and brute-force attacks originating from commercial VPN nodes, often linking to default hostnames like DESKTOP-XXXXXX and WIN-XXXXXX.
Post the internet blackout in Iran in January 2026, similar activities have continued to be observed using IP address ranges from Starlink, which initially provided some operational security for the actors as they operated through commercial VPNs. However, it was noted that the level of operational security diminished following the escalation of conflict, leading to clearer exposure from Iranian IP addresses and even connections through non-VPN channels.
Evidence from some incidents attributed to Handala indicates that network intrusions began months prior to destruction phases, during which persistent access and domain administrator privileges were obtained. Immediately before the destructive activities commenced, access verification using compromised credentials was conducted, with reconnaissance efforts and credential theft alongside.
The attackers executed queries against Active Directory, and actions like dumping memory from the LSASS process indicated potential domain admin rights were achieved.
Lateral Movement and Destructive Payloads
Handala is primarily known for its hands-on approach, conducting lateral movements within compromised networks via Remote Desktop Protocol (RDP). To access hosts that are not directly reachable from outside the network, the deployment of NetBird has been established. This open-source platform creates a secure, private zero-trust mesh network, allowing attackers to facilitate internal connections among multiple systems. After installation across intervening machines, the operators can execute parallel operations across several points, accelerating destruction processes.
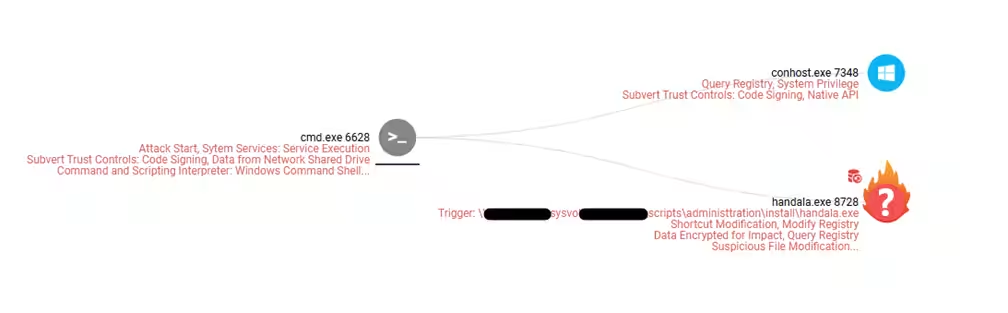
During the destruction phase of the attack, multiple data erasure techniques were employed simultaneously to maximize damage. A significant tool utilized during these operations was the Handala Wiper, distributed through group policy logon scripts as scheduled tasks. This custom wiper causes extensive data loss through file overwriting and MBR-based wipe techniques.
Moreover, the attackers implemented a PowerShell-based custom wiper via group policy scripts that deleted all files within user directories. The structured code and its detailed comments suggest that this PowerShell script may be AI-generated, exacerbating the destruction's breadth. Attacks concluded with the placement of a propaganda image titled

Topics Other)







【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.