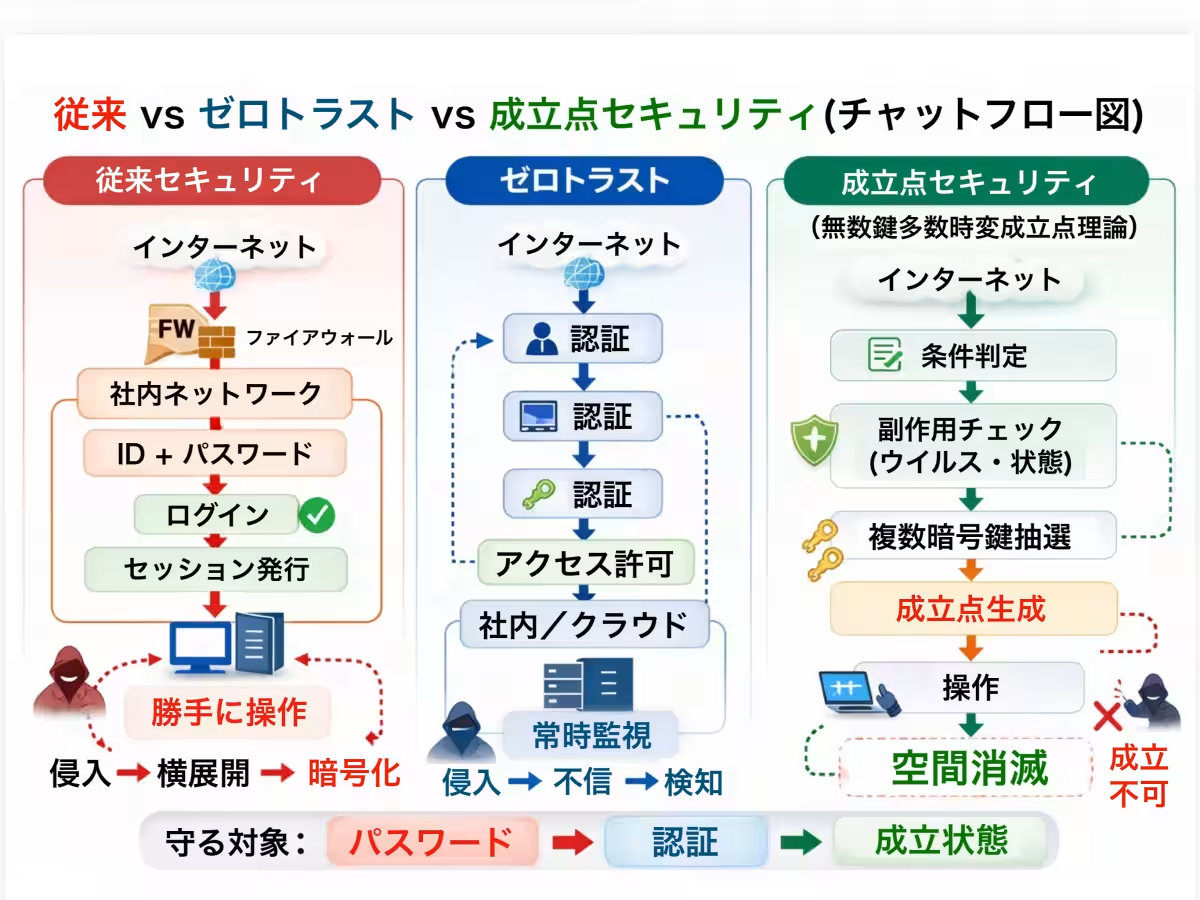
Revolutionizing Security: The Infinite Key Multi-Time Variables Theory Explained
Revolutionizing Security with the Infinite Key Multi-Time Variables Theory
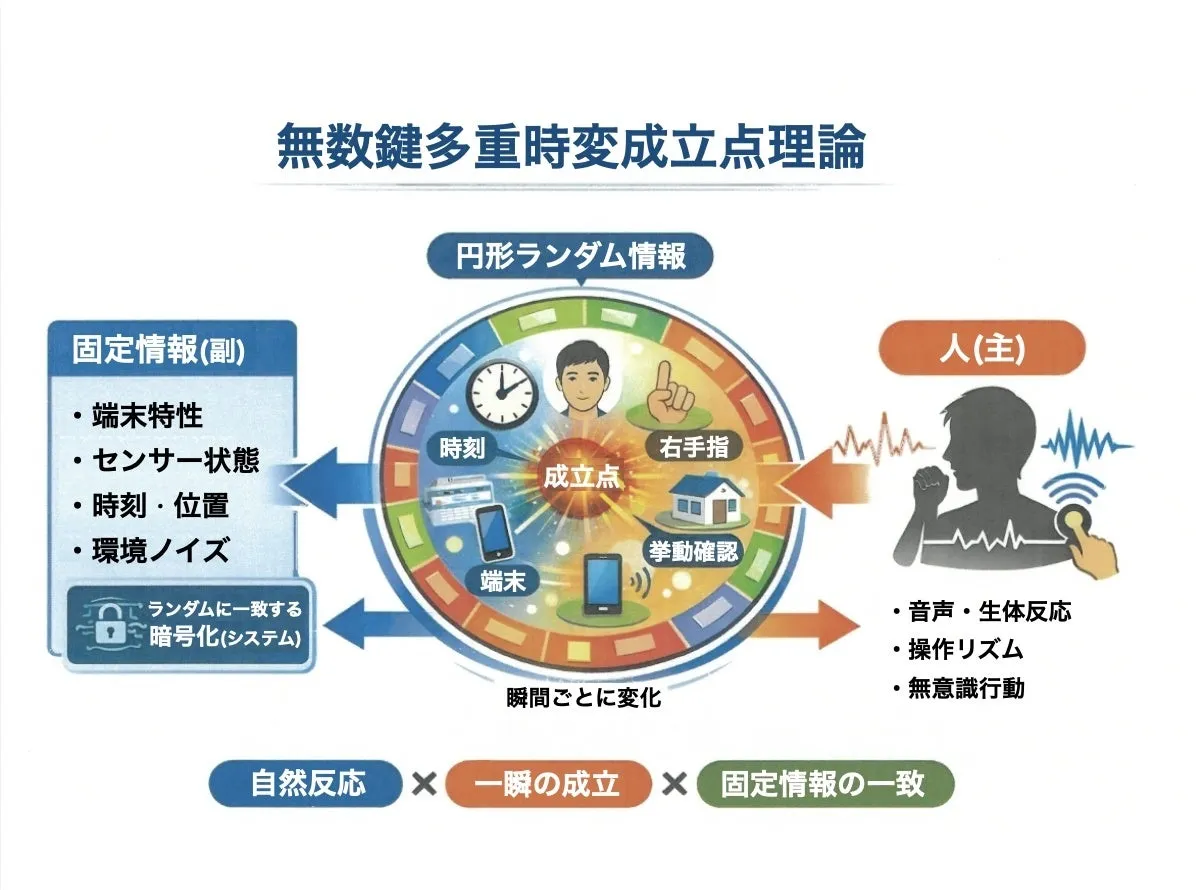
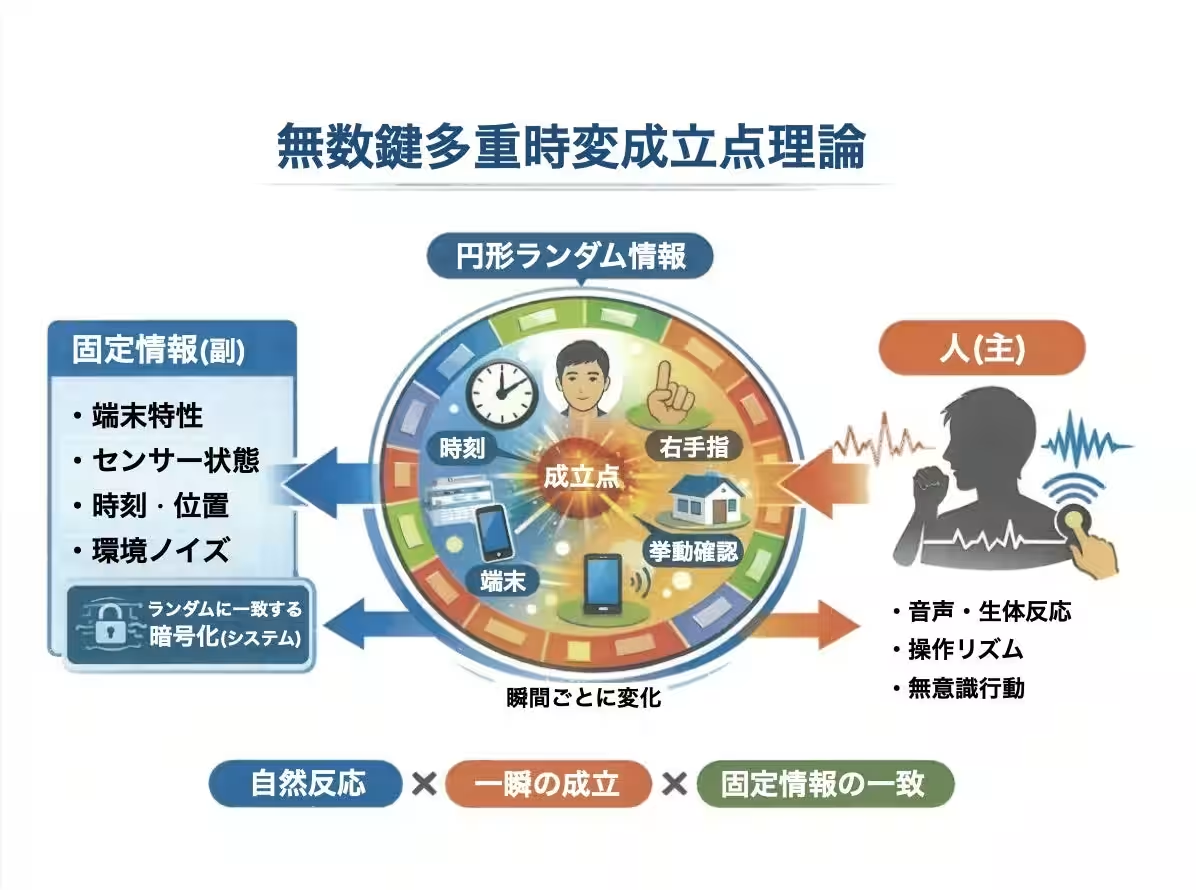
In a world where cyber attacks are becoming more sophisticated and targeted, organizations are under constant threat. With the increasing number of breaches occurring every day, there is an urgent need for an innovative approach to security. Enter the Infinite Key Multi-Time Variables Theory, a groundbreaking concept that promises to redefine the very nature of authentication and security.
The theory was jointly developed by Point Organization, based in Shibuya, Tokyo, and K Trust from Nagoya, and focuses on addressing the inherent weaknesses of traditional security methods. As cyber attackers continue to learn and adapt, the conventional reliance on fixed codes—like passwords and PINs—has become a significant liability.
The Flaws of Traditional Security Methods
Most security systems currently depend on a few critical pieces of data: an ID, a password, and a personal identification number (PIN). Although these methods have helped in securing information, they also showcase serious vulnerabilities:
1. Reusability of Compromised Data: Once leaked, passwords can be reused by attackers multiple times.
2. Unlimited Attempts by Attackers: Cybercriminals can endlessly try different combinations of passwords until they succeed.
3. AI Adaptability: With the development of AI, attackers can now learn from failed attempts and enhance their strategies for future breaches.
The confluence of these issues creates a structure where attackers gain more advantages over time, intensifying the urgency for a new, more effective solution.
A New Framework for Security
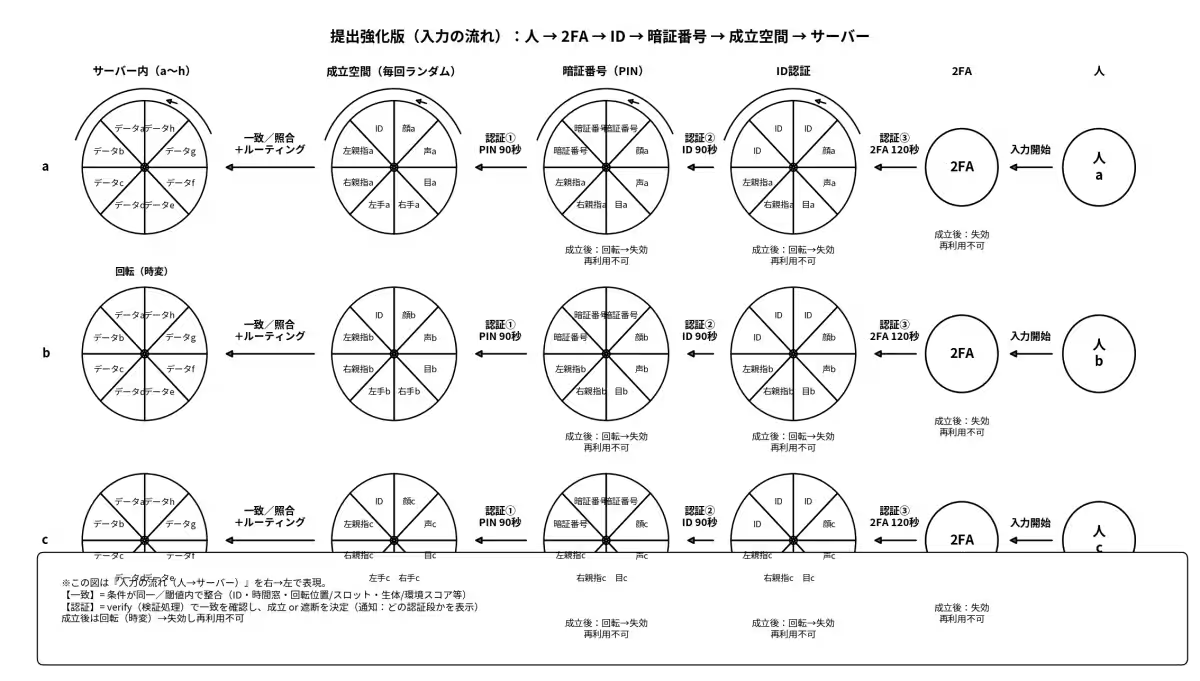
What makes the Infinite Key Multi-Time Variables Theory unique is its departure from fixed answers like IDs and passwords, opting instead for a dynamic and multi-faceted framework.
1. No Need for Memory: The new theory eliminates the requirement for users to remember passwords or IDs. Instead, it leverages natural responses, device states, timestamps, and environmental data to ascertain verification conditions automatically. This significantly eases the user experience, as individuals no longer need to worry about memorizing complex codes.
2. Multiple Authentication Sessions: Unlike traditional login systems where one login corresponds to a single session, this theory introduces multiple entry points. During one login attempt, several separate verification conditions can exist—such as logging in, accessing content, processing payments, or downloading files. This multi-layered security can significantly bolster defenses against unauthorized access.
3. Randomized Key Usage: Instead of relying on a single password, the new system employs countless keys that are drawn randomly for each session. By ensuring that each key can change over time, it becomes exceedingly difficult for attackers to leverage brute-force methods, as they cannot rely on historical data for future access.
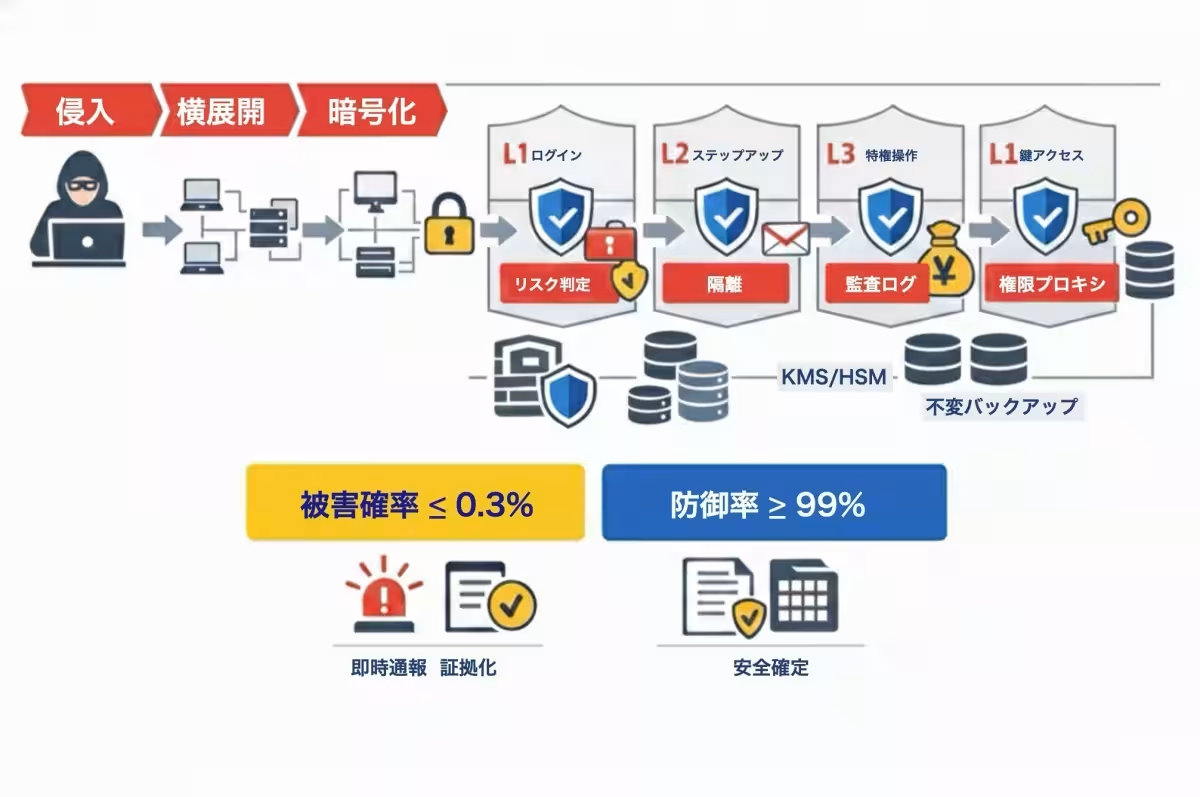
4. Adverse Effects on Attackers: In traditional systems, an attacker can keep trying until they succeed. However, with the new theory in place, if an attacker attempts to breach the system but fails, the system actively fortifies its defenses, making future attacks increasingly difficult.
5. Extensive Threat Modeling: The theory compares results across a massive array of 73 potential attack types, including phishing, AI voice spoofing, deep fakes, and ransomware. In this scenario, the majority of attacks are interrupted before they can finalize a breach.
Performance Metrics
In theoretical applications, initial models suggest that this new framework can achieve a defense rate of over 99% and keep damage probabilities below 0.3%. Although these statistics remain theoretical and require empirical validation, they demonstrate the enormous potential for a shift in how security is approached.
Conclusion: A Paradigm Shift in Security
The fundamental shift encapsulated in the Infinite Key Multi-Time Variables Theory prompts a complete rethinking of security protocols. This approach doesn't merely aim to 'protect the answer'; instead, it recognizes that the essence of security lies in maintaining 'the state of validation'.
In essence, this innovative theory represents a massive leap forward in securing digital interactions, reducing reliance on fixed entries, and aiming for an unprecedented level of security efficacy, making it a pertinent solution in today's digital landscape. Expect further developments and educational resources as this theory moves toward social application in upcoming videos and reports.
For additional insights on the Infinite Key Multi-Time Variables Theory, you can view introductory videos explaining the essence, theory, and applications at:
This breakthrough in cybersecurity not only promises enhanced protection for corporations and governments but also paves the way for a future where digital security becomes seamless and intuitive.







Topics Consumer Technology)






【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.