

Check Point Releases 2025 Report on Cybersecurity Threats in Manufacturing
Check Point's New Report on Cybersecurity Risks in Manufacturing for 2025
On April 13, 2026, Check Point Software Technologies Ltd., a leading company in cybersecurity solutions, released the 'Manufacturing Threat Landscape 2025' report. This document sheds light on the evolving cybersecurity threat landscape within the manufacturing sector, detailing alarming trends and statistics surrounding ransomware and supply chain attacks.
Major Findings
One of the most shocking revelations from the report is that the manufacturing industry has become the primary target for ransomware attacks on a global scale. In 2025, there were a staggering 7,419 ransomware incidents worldwide, marking a 32% increase from previous years. Among these, attacks on manufacturing surged by 56%, escalating to 1,466 incidents. This alarming trend emphasizes that attackers are increasingly recognizing the economic vulnerabilities within the industry, where production halts can lead to losses amounting to millions of dollars per day. These financial motivations are influencing the tactics threat actors employ, often using downtime as leverage in negotiations for ransom payments.
The United States led in ransomware incidents within the manufacturing sector, accounting for 713 attacks. Following were countries like India, Germany, the UK, and Canada, demonstrating that cyber threats are a global issue affecting both industrialized and emerging nations alike.
Adding to the challenges, supply chain attacks nearly doubled from 154 incidents in 2024 to 297 in 2025. Cybercriminals are exploiting smaller vendors and service providers as entry points to infiltrate larger manufacturing firms, showcasing a worrying trend towards targeting the interconnectivity of the production line.
Reasons for Vulnerability in Manufacturing
The report outlines three major structural vulnerabilities exacerbating cyber risks in manufacturing:
1. Legacy Operational Technology (OT) Systems: Many manufacturing processes rely on outdated systems that were not designed with modern cybersecurity in mind. In Europe, for instance, around 80% of manufacturers operate essential OT systems rife with known vulnerabilities, making them easy targets for exploitation.
2. Complex Supply Chains: As supply chain operations become more intricate, the attack surface expands, making it easier for threat actors to locate and exploit weaknesses from less protected suppliers.
3. Ransomware-as-a-Service (RaaS): The rise of affiliate-based operational models enables rapid proliferation of attacks, resource sharing, and targeted campaigns tailored to specific regions and industries.
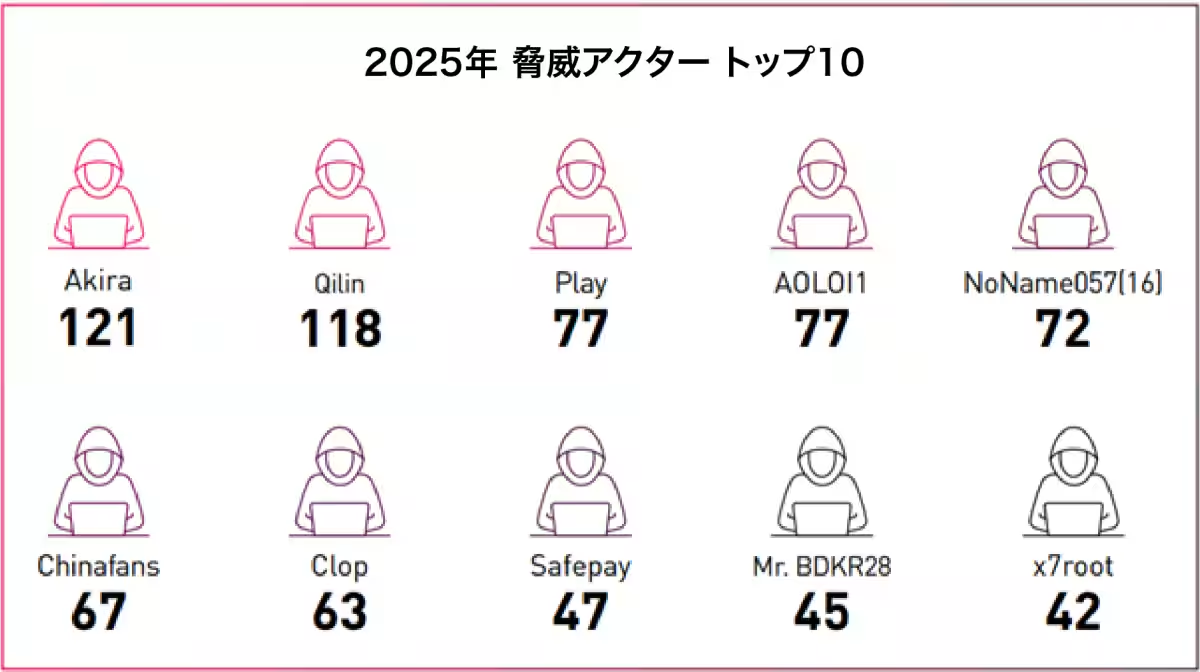
Leading Threat Actors
In 2025, multiple ransomware groups emerged as primary perpetrators of cyber attacks in the manufacturing sector. One such group, "Akira," gained notoriety for its economic success, projected to generate revenues around $244 million by year's end. Their approaches often involve exploiting unprotected VPNs and phishing attacks. An incident in 2025 saw the group compromise a German cable manufacturer, leaking 27 GB of sensitive data before encryption.
Another group, "Qilin," based in Russia, concentrated on the manufacturing and logistics sectors, stealing nearly 30,000 internal files in one notable attack, further jeopardizing continuous supply chain operations.
Meanwhile, the group "Play" continued to impact US manufacturers, with FBI reports indicating that approximately 900 organizations suffered breaches in the first half of 2025 due to their notorious methods of exploiting valid credentials.
Additionally, geopolitical actors like the hacking group "NoName057(16)" have targeted industrial organizations, deploying various attacks and digital disruptions during times of rising geopolitical tension.
Common Intrusion Methods
Ransomware was linked to 890 incidents in the manufacturing sector in 2025, but several other vectors were utilized:
- - Exploiting Vulnerabilities (32% of Incidents): Outdated OT systems and public applications were among the most targeted.
- - Phishing and Malicious Email Campaigns (23%): Enhanced by AI-generated lures turned more sophisticated.
- - Compromised Credentials: Stolen credential services were traded in black markets, commanding prices from $4,000 to $70,000.
- - Supply Chain Compromise, Remote Access Exploitation: Attackers maneuvered undetected between IT and OT environments.
These findings highlight a transition from singular vectors to broader attack strategies, where threats like data theft and sabotage are becoming increasingly common.
Regional Impacts
In the third quarter of 2025, 72% of ransomware attacks on industrial sectors in Europe targeted manufacturers, with average ransom demands soaring to $1.16 million, more than double the previous year's figures. Notably, incidents in industries such as automotive and aerospace created widespread disruptions across various countries.
The United States continued to bear the brunt of attacks, marking the fourth consecutive year in which manufacturing was the most attacked sector, with nearly half of industrial security breaches attributed to ransomware. The median cost of such attacks was reported to be around $500,000, excluding long-term operational losses.
In India, the manufacturing sector became the epicenter of ransomware attacks in the APAC region, with 65% of affected businesses paying ransoms averaging about $1.35 million.
Reevaluating Cybersecurity Priorities
The 2025 threat landscape makes it essential for the manufacturing sector to reassess its cybersecurity strategies:
1. Implementing Zero Trust Architectures: Enforcing strict identity verification and minimizing access can bolster defenses.
2. Vulnerability Management and Patching: The necessity for rapid vulnerability remediation, especially on exposed platforms, remains paramount.
3. Credential Management: Strengthening detection mechanisms for leaked credentials and enhancing SSO/MFA implementations.
4. Immutable Offline Backups: To defend against attacks targeting backup infrastructures.
5. Employee Training and Awareness: With evolving phishing attacks powered by AI, continuous training is crucial.
6. Third-Party Risk Management: As vendors and third-party services become vectors for attacks, their management is now a critical function in cybersecurity.
Outlook for 2026
Based on the current trajectory, the manufacturing sector is expected to face heightened cyber threats in 2026, characterized by the rise of AI-assisted ransomware and faster attack execution timelines. For more detailed insights, refer to the 'Manufacturing Threat Landscape 2025' report.
For additional information on Check Point Software Technologies, visit Check Point. They are dedicated to securing over 100,000 organizations globally, focusing on promoting safe AI transformations and mitigating cyber risks through an agile security architecture.


Topics Business Technology)







【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.