

Revolutionizing Security: The Infinite Key Multi-Dimensional Theory Unveiled
Introducing the Infinite Key Multi-Dimensional Theory
In an unprecedented announcement on March 24, 2026, Point Organization Inc. partnered with K Trust to unveil a revolutionary security concept. This new approach, termed the Infinite Key Multi-Dimensional Theory, offers a game-changing alternative to traditional security measures, particularly in a world that demands enhanced protective frameworks. The theory presents a zero-trust evolution that requires no passwords, promising a future filled with security possibilities.
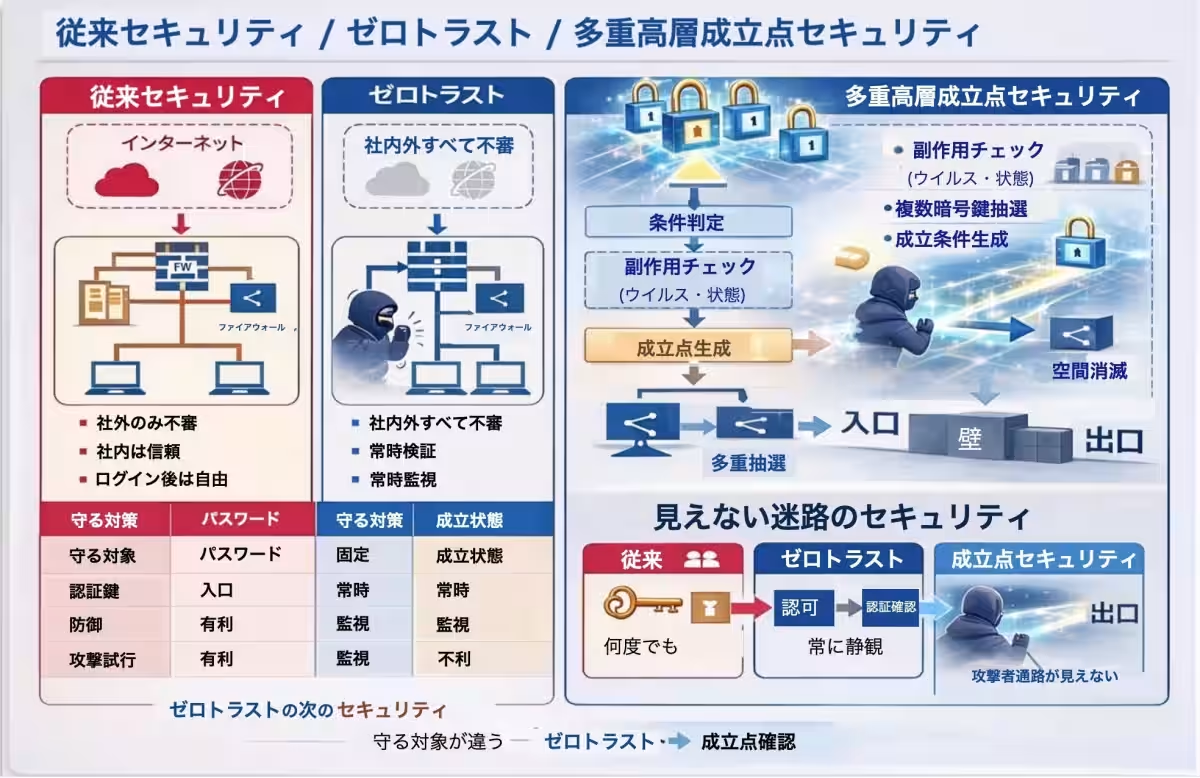
The Current Security Landscape
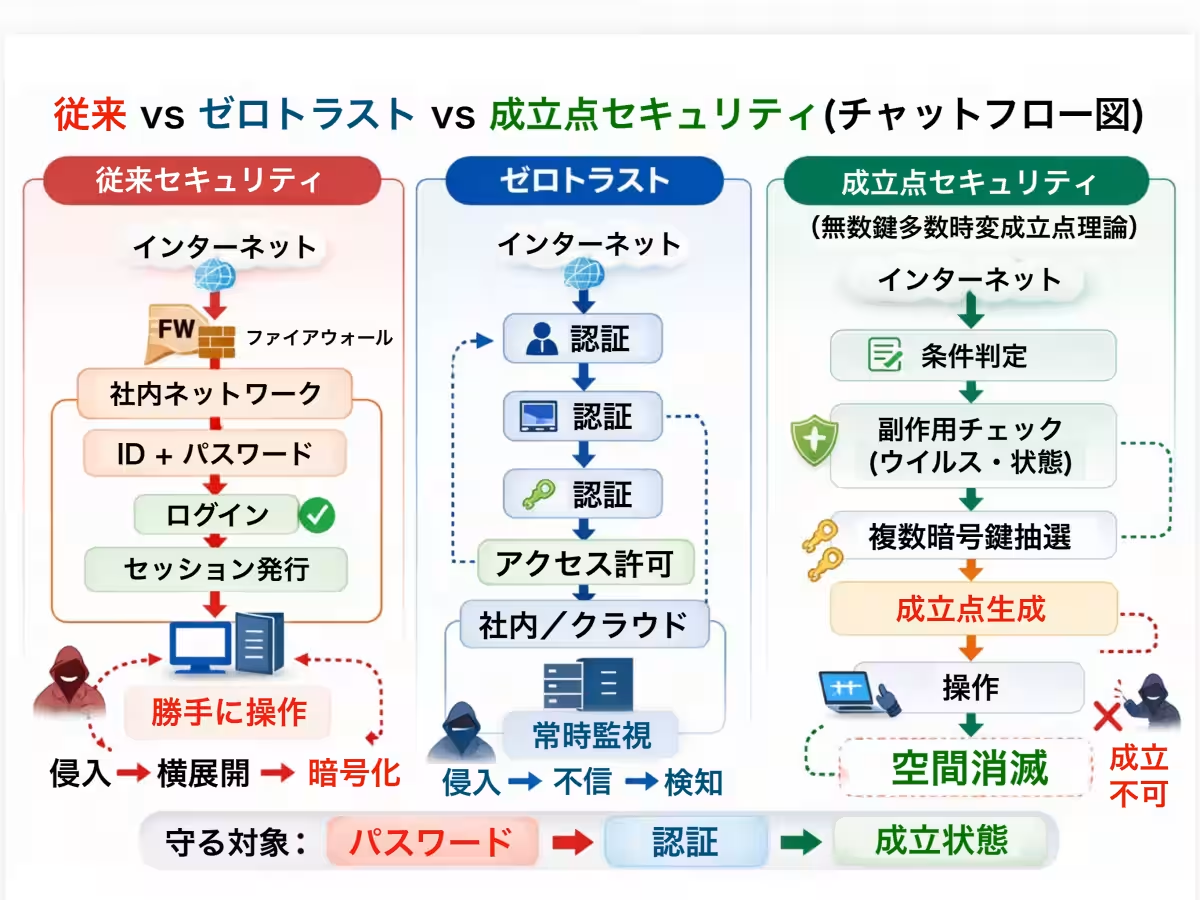
Historically, security systems have relied heavily on fixed identifiers such as IDs, passwords, and keys. Once a hacker breaches these systems, they can exploit vulnerabilities and gain access across multiple networks. The reliance on static credentials creates significant risks, allowing cybercriminals to execute malicious actions post-authentication.
Zero-trust protocols were introduced to combat such threats by ensuring constant authentication and continuous monitoring. However, even zero-trust systems face limitations due to persistent, fixed credentials that can still be compromised.
The Birth of a New Security Paradigm
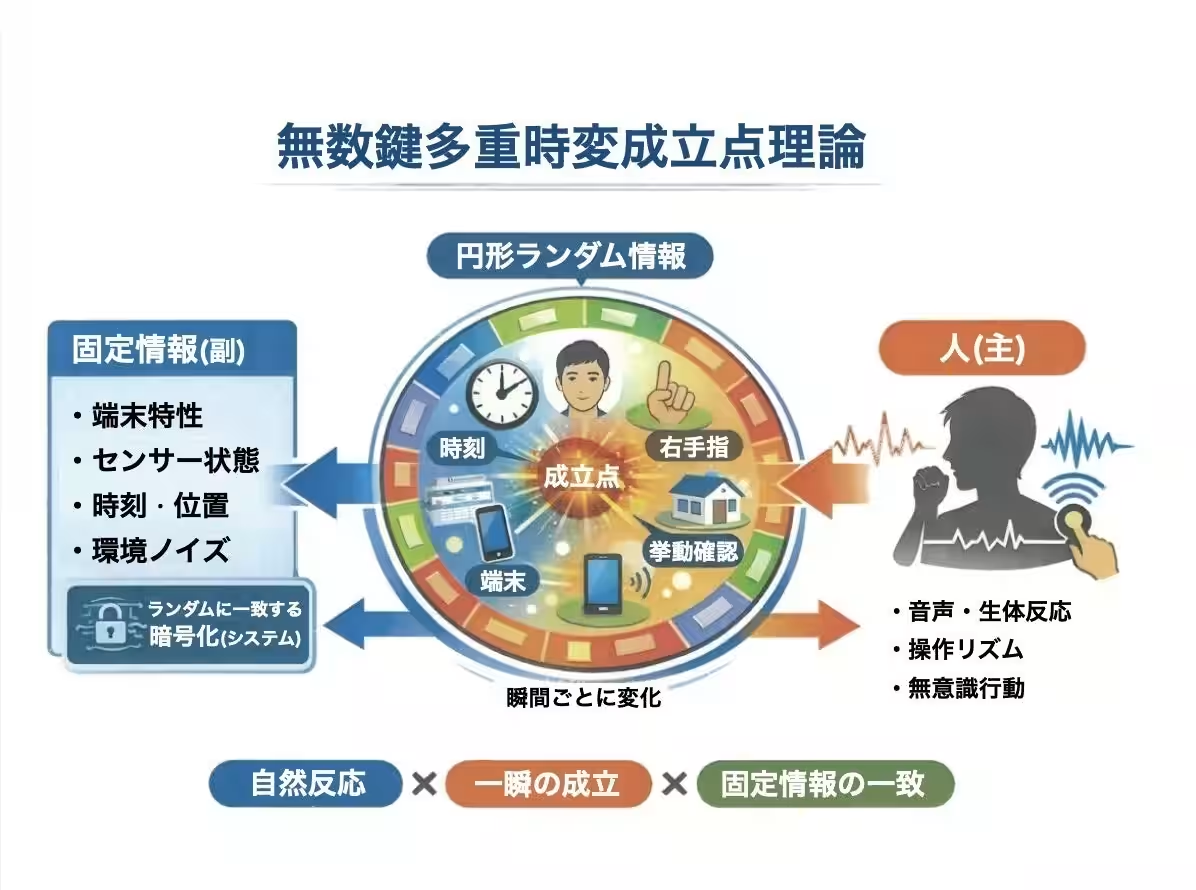
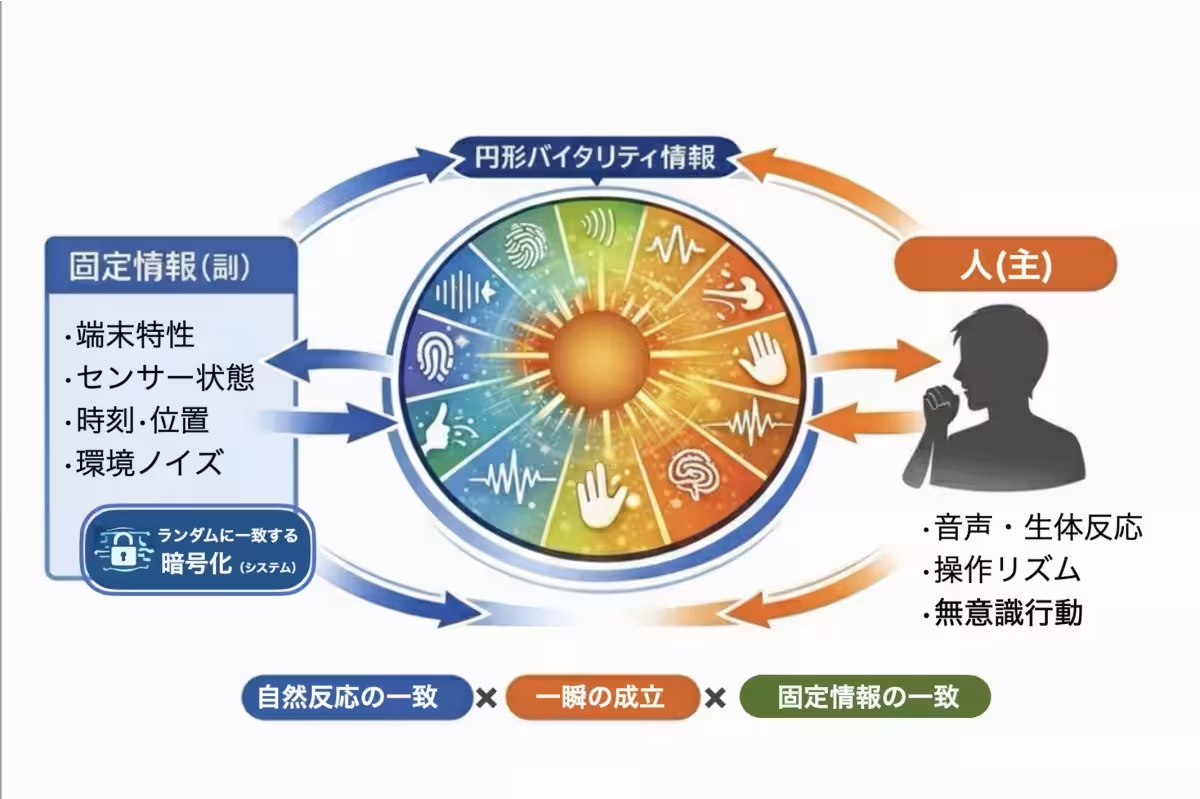
The Infinite Key Multi-Dimensional Theory aims to address the shortcomings of traditional and zero-trust security frameworks. It utilizes a novel concept that minimizes time-bound expressions of authentication. Essentially, access is granted only for the briefest moments required for operations. This leads to a fundamentally different security landscape:
Key Features of the Theory
1. No Fixed Keys: The encryption keys are temporary, random, and unique for each session, eliminating the risk of re-use and related vulnerabilities.
2. Layered Multi-Dimensional Structure: This new model incorporates five layers, each responsible for different aspects of security, including user verification, virus detection, and the generation of cryptographic keys.
3. Immediate Termination: The established conditions self-terminate post-usage, leaving no opportunity for potential exploit during subsequent attempts.
4. AI Integration: The multi-layered structure incorporates three levels of automated AI defenses that continuously check for unusual behavior, ensuring that the operation can only proceed in a safe environment.
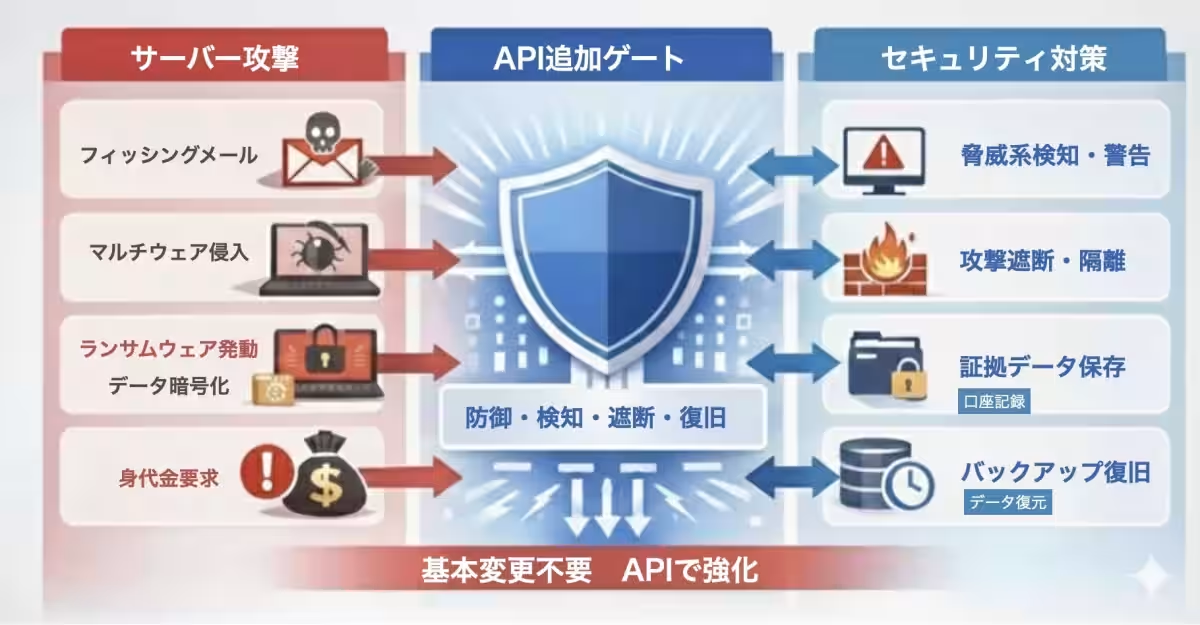
Transforming the Approach to Cyber Threats
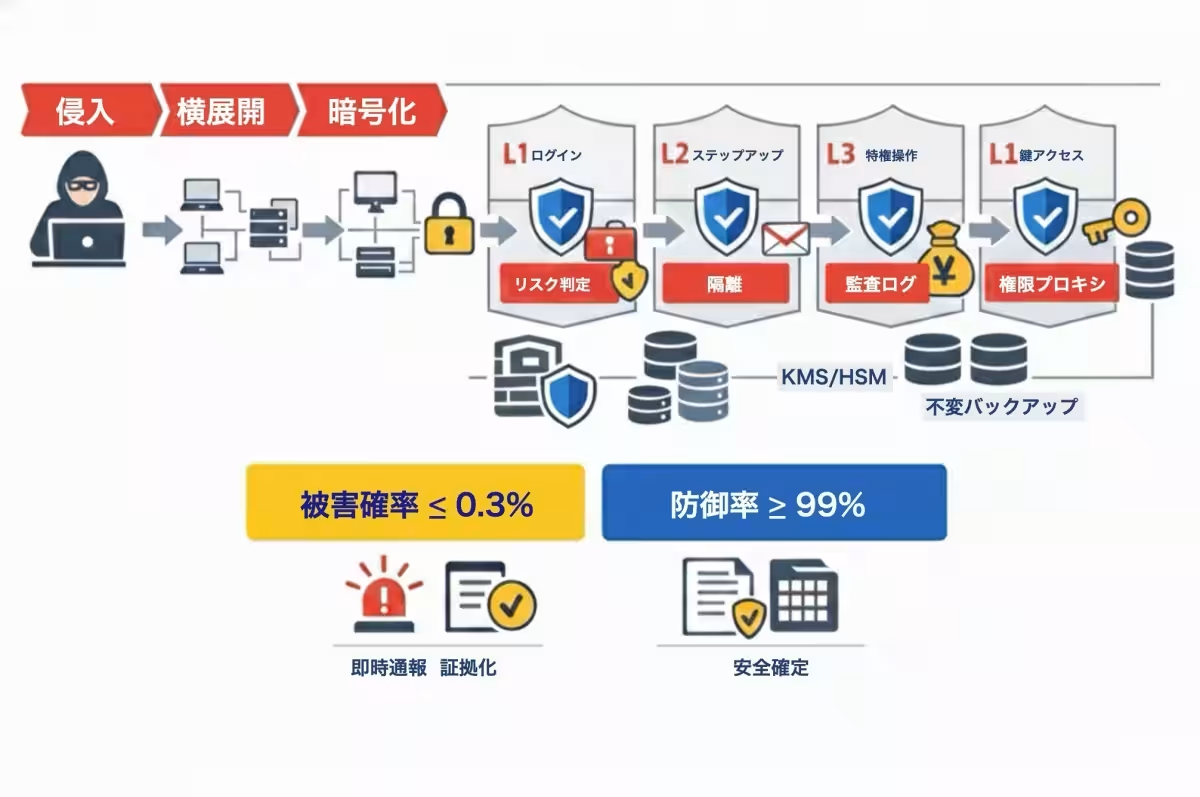
In contrast to traditional security models, the Infinite Key structure requires multiple verifications before access is granted—making it astronomically harder for hackers to penetrate systems. The operational flow resembles:
1. Intrusion attempts lead to initial verification.
2. Each layer conducts thorough checks before granting access to the next encryption key.
3. Abnormal behaviors collapse the session before it completes.
This methodological approach alters the attack model significantly. Instead of simply breaking through a single point of entry, attackers must navigate through multiple complex layers that instantaneously react to threats.
Ransomware Protection
The evolving cyber threat landscape has seen a marked rise in ransomware attacks, which depend heavily on obtaining execution rights. The Infinite Key Theory blocks privileges and conditions that enable such attacks, maintaining operational security throughout the process. Evidence shows that the theoretical defense rate exceeds 99.7%, a dramatic improvement over conventional defenses.
A Vision for the Future
Point Organization Inc. and K Trust envisage a future where security is not just an afterthought but a fundamental aspect of technology. The Infinite Key Multi-Dimensional Theory positions itself at the forefront, advocating for a security architecture that evolves in pace with cyber threats. It allows for seamless authentication without the burden of remembering and managing passwords.
The journey from traditional to next-gen security is underway, and this innovative theory could very well be its guiding light. As the world continues to generate vast amounts of sensitive data, the demand for such robust and flexible security measures will only grow stronger.
For further information and resources on this groundbreaking theory, visit here. Explore detailed comparisons through our curated YouTube series that showcases the theory’s advantages over existing models.
About Point Organization Inc.
Point Organization Inc., established in December 2021, aims to enhance the wealth and security of nations and citizens alike. Led by CEO Yuki Takeuchi, the organization works relentlessly towards a secure future.
- ---
To learn more, visit our official website. For media inquiries, please contact:
- - Yuki Takeuchi at [email protected]
About K Trust
K Trust, founded by Tomoko and Kazunori Hirakawa, is dedicated to providing innovative solutions for the future through its array of products.
For additional insights, contact:
- - Tomoko Hirakawa at [email protected]
Together, these organizations are reshaping the realm of security, inviting a new era of protection without the constraints of traditional systems.





Topics Consumer Technology)










【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.