
Comprehensive Overview of AI Agent Security Threats Published by CORe Inc.
Comprehensive Overview of AI Agent Security Threats
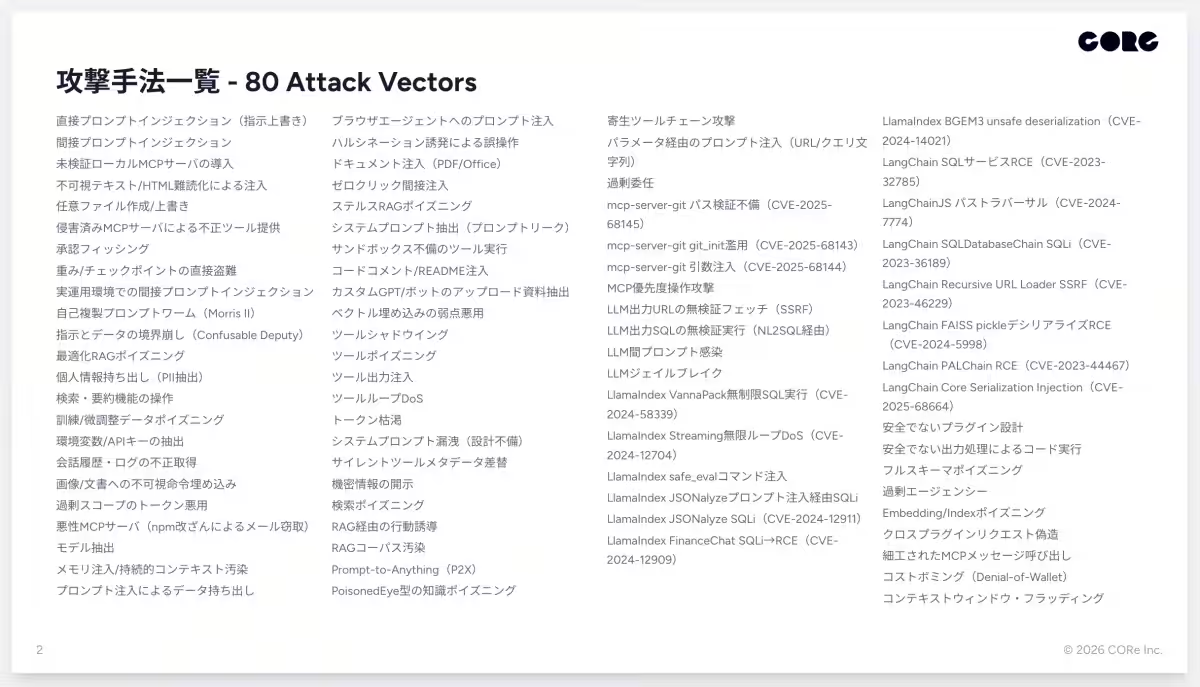
On March 17, 2026, CORe Inc., based in Shinjuku, Tokyo, released a thorough report titled "AI Agent Attack Techniques and Countermeasures (March 2026 Edition)." This comprehensive study encompasses 80 different attack methods specifically targeting AI agents, along with preventive, detection, and response strategies, all within a total of 164 pages.
Background of the Report
As the utilization of AI agents in business processes intensifies, especially following the latter half of 2025, new threats have emerged, including prompt injection attacks, MCP server breaches, and RAG corpus contamination. Notably, relevant vulnerabilities are accumulating in databases managed by organizations like OWASP (Open Worldwide Application Security Project) and NIST (National Institute of Standards and Technology). The vast array of attack methods necessitated the creation of a resource that enables developers and security personnel to have a holistic understanding of these threats.
In targeting AI systems, the most vulnerable area is not the AI models themselves, such as GPT or Gemini. Instead, the significant weak point lies in the context pipeline – the route through which user questions and external data are passed to the AI. While the security of the AI models is strongly protected by their developers, the management of what data gets input into these models is largely left to application developers, hence creating potential vulnerabilities.
Report Overview and Features
This 164-page document catalogues 80 unique attack methods against AI agents in an organized manner. Each method is accompanied by a description of the attack, as well as a structured approach outlining preventive, detection, and response strategies. This makes it readily usable as a checklist during security reviews or incident responses.
The main categories covered in the report include:
- - Prompt Injection Techniques: Direct, indirect, image embedding, zero-click, document injection, among 16 types.
- - MCP Server/Tool Attacks: Such as unverified server deployments, Tool Poisoning, Tool Shadowing, and Full-Schema Poisoning that account for 14 types.
- - RAG/Knowledge Base Contamination: Including optimized RAG poisoning, stealth RAG poisoning, and Retrieval Poisoning, among 8 types.
- - Information Leakage/Data Extraction: With 10 types including PII extraction, Memory Poisoning, and environment variable theft.
- - Output Misuse/Downstream System Breaches: Covering arbitrary file creation, SSRF, and SQL injection chains, totaling 12 types.
- - DoS/Cost Attacks: Including Tool Loop DoS, Token Exhaustion, Cost Bombing, and Context Window Flooding spanning 6 types.
- - Framework-Specific Vulnerabilities: Including 14 known CVEs related to LlamaIndex, LangChain, and mcp-server-git.
Each attack method includes an evidence level (research validation, public disclosures of actual damage, vulnerability advisories, guidance/conceptual proofs) designed to help prioritize response efforts. In addition, specific URLs for cited research, OWASP guidelines, and references from the National Vulnerability Database (NVD) are included within the document for further scrutiny.
Target Audience
This report is intended primarily for engineers, security architects, and auditors involved in the development and operation of AI agents, as well as information systems and corporate planning departments promoting AI adoption. Additionally, it is aimed at SRE teams and infrastructure personnel developing MCP servers and RAG pipelines.
About CORe Inc.
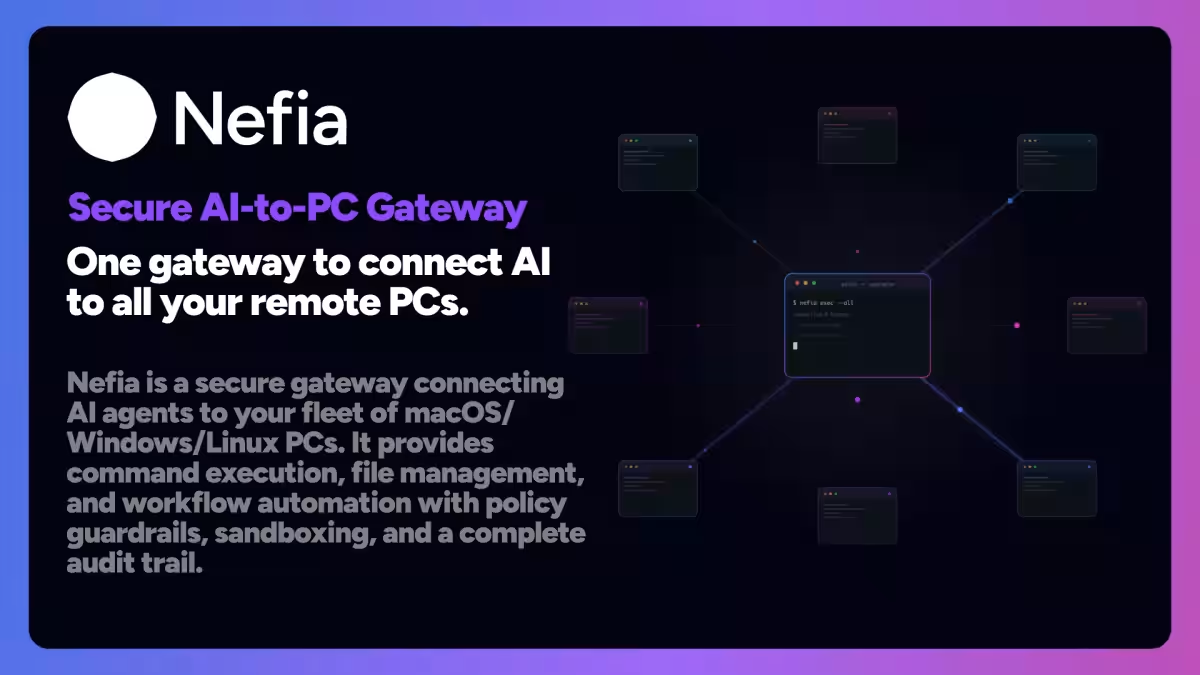
CORe Inc. is a company focused on developing generic AI products. They offer a range that includes Browser Use AI called "Copelf," an all-in-one utility AI that resides on desktops named "IrukaDark," and a secure gateway named "Nefia" designed to manage remote PC environments via AI agents. Leveraging their technological prowess, CORe also provides AI consulting services for businesses.
Company Profile
Name: CORe Inc.
Established: May 17, 2017
Location: 18th Floor, JR Shinjuku Miraina Tower, 4-1-6 Shinjuku, Tokyo
CEO: Masato Okubaki
CTO: Naoto Ikeda
URL: CORe Inc. Website

Topics Other)










【About Using Articles】
You can freely use the title and article content by linking to the page where the article is posted.
※ Images cannot be used.
【About Links】
Links are free to use.